- browser as a service (BaaS)
- infrastructure as a service (IaaS)
- software as a service (SaaS)
- wireless as a service (WaaS)
2. For a data center, what is the difference in the server virtualization data traffic compared with the traditional client-server model?
- Data traffic from clients will be routed to multiple virtual servers.
- There are significant data exchanges between virtual servers.
- There is more data traffic flowing from virtual servers to clients.
- More network control traffic is generated between virtual servers and clients.
3. Which component in a traditional infrastructure device provides Layer 2 and Layer 3 functions to create data paths within a network?
- data plane
- control plane
- adjacency table
- forwarding information base
4. Which network traffic management technology is a basic element in SDN implementations?
- OpenFlow
- OpenStack
- IEEE 802.1aq
- Interface to the Routing System
5. Which type of hypervisor would most likely be used in a data center?
- Type 2
- Type 1
- Nexus
- Hadoop
6. Which is a characteristic of a Type 1 hypervisor?
- installed directly on a server
- best suited for consumers and not for an enterprise environment
- does not require management console software
- installed on an existing operating system
7. Which two layers of the OSI model are associated with SDN network control plane functions that make forwarding decisions? (Choose two.)
- Layer 1
- Layer 2
- Layer 3
- Layer 4
- Layer 5
8. What pre-populates the FIB on Cisco devices that use CEF to process packets?
- the routing table
- the adjacency table
- the ARP table
- the DSP
9. What is a function of the data plane of a network device?
- sending information to the CPU for processing
- building the routing table
- resolving MAC addresses
- forwarding traffic flows
10. Which statement describes the concept of cloud computing?
- separation of application from hardware
- separation of management plane from control plane
- separation of operating system from hardware
- separation of control plane from data plane
11. Which cloud model provides services for a specific organization or entity?
- a public cloud
- a hybrid cloud
- a private cloud
- a community cloud
12. What two benefits are gained when an organization adopts cloud computing and virtualization? (Choose two.)
- provides a “pay-as-you-go” model, allowing organizations to treat computing and storage expenses as a utility
- enables rapid responses to increasing data volume requirements
- distributed processing of large data sets in the size of terabytes
- elimination of vulnerabilities to cyber attacks
- increases the dependance on onsite IT resources
13. Which type of Hypervisor is implemented when a user with a laptop running the Mac OS installs a Windows virtual OS instance?
- type 2
- virtual machine
- type 1
- bare metal
14. A small company is considering moving many of its data center functions to the cloud. What are three advantages of this plan? (Choose three.)
- The company only needs to pay for the amount of processing and storage capacity that it uses.
- Cloud services are billed at a fixed fee no matter how much processing and storage are used by the company.
- The company does not need to be concerned about how to handle increasing data storage and processing demands with in-house data center equipment.
- The company can increase processing and storage capacity as needed and then decrease capacity when it is no longer needed.
- Single-tenant data centers can easily grow to accommodate increasing data storage requirements.
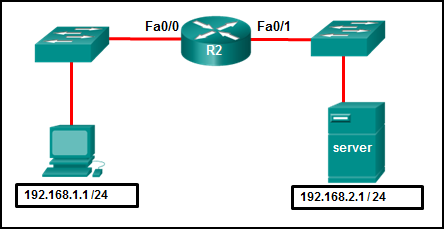
- Cloud services enable the company to own and administer its own servers and storage devices.
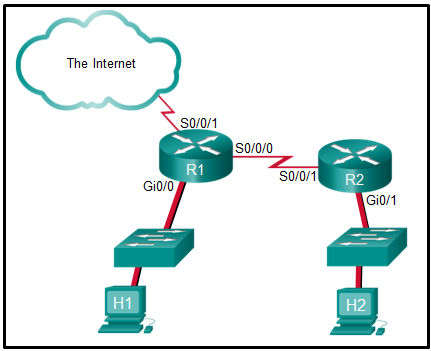
15. How does virtualization help with disaster recovery within a data center?
- support of live migration
- guarantee of power
- improvement of business practices
- supply of consistent air flow
16. What technology allows users to access data anywhere and at any time?
- Cloud computing
- virtualization
- micromarketing
- data analytics
17. Which action takes place in the assurance element of the IBN model?
- verification and corrective action
- configuring systems
- translation of policies
- integrity checks
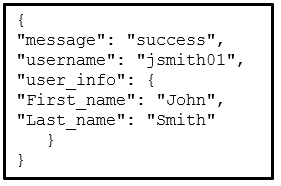
18. Refer to the exhibit. Which data format is used to represent the data for network automation applications?
- XML
- YAML
- HTML
- JSON
19. What is the function of the key contained in most RESTful APIs?
- It is the top-level object of the API query.
- It is used to authenticate the requesting source.
- It represents the main query components in the API request.
- It is used in the encryption of the message by an API request.
20. Which two configuration management tools are developed using Ruby? (Choose two.)
- Puppet
- Ansible
- SaltStack
- Chef
- RESTCONF
21. Which term is used to describe a set of instructions for execution by the configuration management tool Puppet?
- Playbook
- Cookbook
- Manifest
- Pillar
22. Which term is used to describe a set of instructions for execution by the configuration management tool SaltStack?
- Cookbook
- Manifest
- Pillar
- Playbook
23. Which scenario describes the use of a public API?
- It requires a license.
- It can be used with no restrictions.
- It is used between a company and its business partners.
- It is used only within an organization.
24. What is YAML?
- It is a scripting language.
- It is a data format and superset of JSON.
- It is a compiled programming language.
- It is a web application.
25. Which RESTFul operation corresponds to the HTTP GET method?
- post
- patch
- update
- read
26. Which technology virtualizes the network control plane and moves it to a centralized controller?
- SDN
- fog computing
- cloud computing
- IaaS
27. What are two functions of hypervisors? (Choose two.)
- to partition the hard drive to run virtual machines
- to manage virtual machines
- to protect the host from malware infection from the virtual machines
- to share the antivirus software across the virtual machines
- to allocate physical system resources to virtual machines
28. What is a difference between the functions of Cloud computing and virtualization?
- Cloud computing requires hypervisor technology whereas virtualization is a fault tolerance technology.
- Cloud computing separates the application from the hardware whereas virtualization separates the OS from the underlying hardware.
- Cloud computing provides services on web-based access whereas virtualization provides services on data access through virtualized Internet connections.
- Cloud computing utilizes data center technology whereas virtualization is not used in data centers.
29. How is the YAML data format structure different from JSON?
- It uses indentations.
- It uses end tags.
- It uses hierarchical levels of nesting.
- It uses brackets and commas.
30. What is the most widely used API for web services?
- XML-RPC
- SOAP
- JSON-RPC
- REST
31. What is REST?
- It is a way to store and interchange data in a structured format.
- It is an architecture style for designing web service applications.
- It is a human readable data structure that is used by applications for storing, transforming, and reading data.
- It is a protocol that allows administrators to manage nodes on an IP network.
32. What is a difference between the XML and HTML data formats?
- XML does not use predefined tags whereas HTML does use predefined tags.
- XML encloses data within a pair of tags whereas HTML uses a pair of quotation makes to enclose data.
- XML formats data in binary whereas HTML formats data in plain text.
- XML does not require indentation for each key/value pair but HTML does require indentation.
33. To avoid purchasing new hardware, a company wants to take advantage of idle system resources and consolidate the number of servers while allowing for multiple operating systems on a single hardware platform. What service or technology would support this requirement?
- dedicated servers
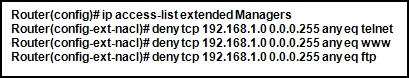
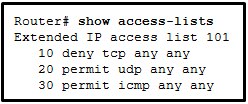
- Cisco ACI
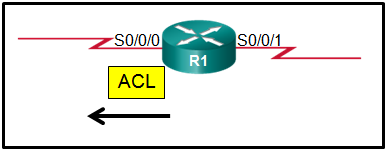
- virtualization
- software defined networking
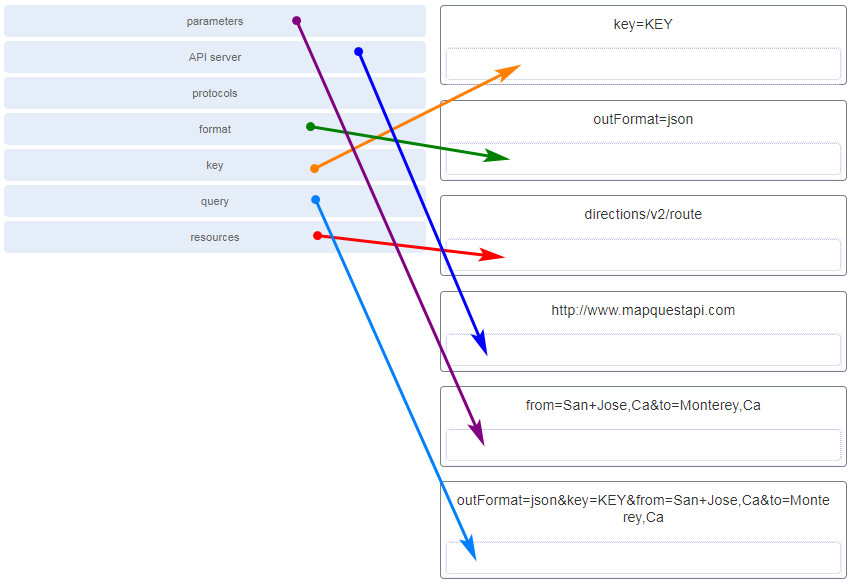
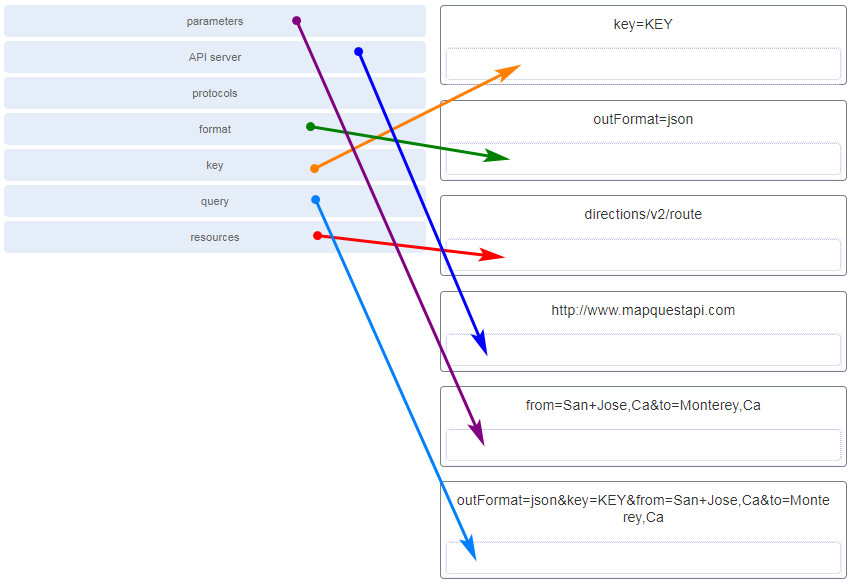
34. Match the term to the RESTful API request http://www.mapquestapi.com/directions/v2/route?outFormat=json&key=KEY&from=San+Jose,Ca&to=Monterey,Ca component. (Not all options are used.)
35. Which cloud computing opportunity would provide the use of network hardware such as routers and switches for a particular company?
- software as a service (SaaS)
- wireless as a service (WaaS)
- infrastructure as a service (IaaS)
- browser as a service (BaaS)
36. What component is considered the brains of the ACI architecture and translates application policies?
- the Application Network Profile endpoints
- the Nexus 9000 switch
- the hypervisor
- the Application Policy Infrastructure Controller
37. Which statement describes the concept of cloud computing?
- separation of management plane from control plane
- separation of control plane from data plane
- separation of application from hardware
- separation of operating system from hardware
38. In which situation would a partner API be appropriate?
- an internet search engine allowing developers to integrate the search engine into their own software applications
- company sales staff accessing internal sales data from their mobile devices
- someone creating an account on an external app or website by using his or her social media credentials
- a vacation service site interacting with hotel databases to display information from all the hotels on its web site
39. Because of enormous growth in web traffic, a company has planned to purchase additional servers to help handle the web traffic. What service or technology would support this requirement?
- virtualization
- data center
- cloud services
- dedicated servers
40. What is the term used to indicate a variation of delay?
- latency
- serialization delay
- speed mismatch
- jitter
41. A network engineer performs a ping test and receives a value that shows the time it takes for a packet to travel from a source to a destination device and return. Which term describes the value?
- jitter
- latency
- priority
- bandwidth
42. What role do network devices play in the IntServ QoS model?
- Network devices ensure that resources are available before traffic is allowed to be sent by a host through the network.
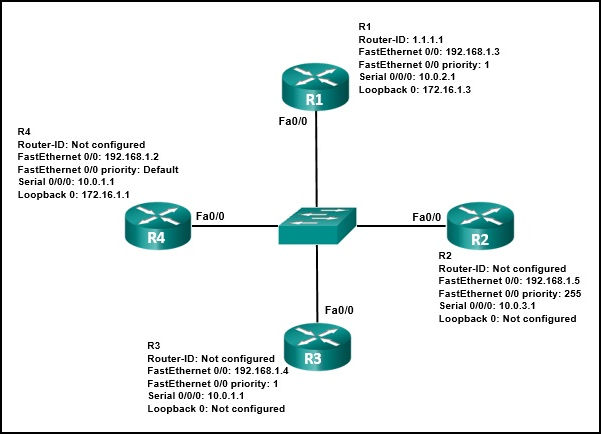
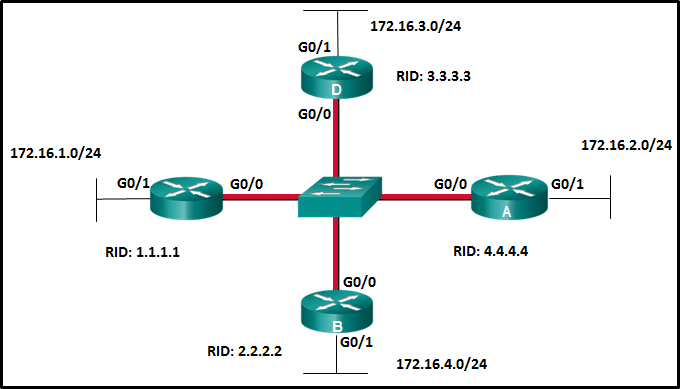
- Network devices provide a best-effort approach to forwarding traffic.
- Network devices are configured to service multiple classes of traffic and handle traffic as it may arrive.
- Network devices use QoS on a hop-by-hop basis to provide excellent scalability.
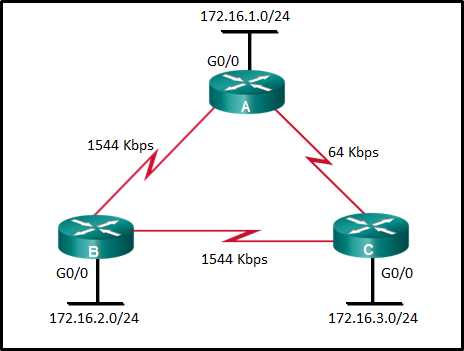
43. Which device would be classified as a trusted endpoint?
- switch
- router
- firewall
- IP phone
44. What is the benefit of deploying Layer 3 QoS marking across an enterprise network?
- Layer 3 marking can carry the QoS information end-to-end.
- Layer 3 marking can carry QoS information on switches that are not IP aware.
- Layer 3 marking can be carried in the 802.1Q fields.
- Layer 3 marking can be used to carry non-IP traffic.
45. What is the function of a QoS trust boundary?
- A trust boundary identifies the location where traffic cannot be remarked.
- A trust boundary only allows traffic to enter if it has previously been marked.
- A trust boundary identifies which devices trust the marking on packets that enter a network.
- A trust boundary only allows traffic from trusted endpoints to enter the network.
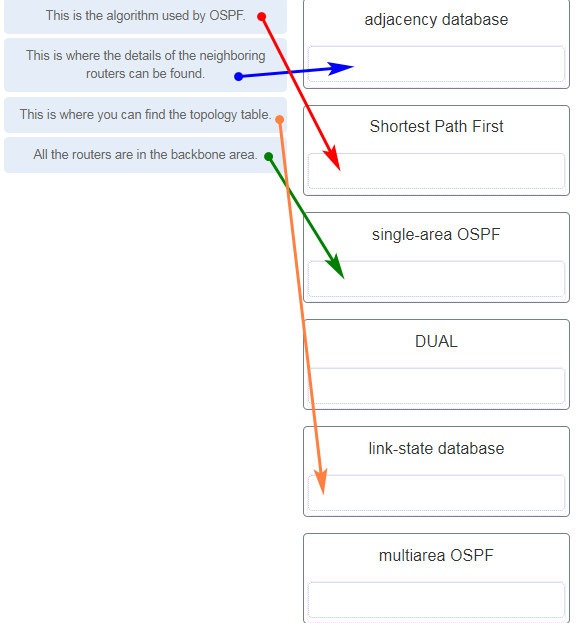
46. What are two approaches to prevent packet loss due to congestion on an interface? (Choose two.)
- Decrease buffer space.
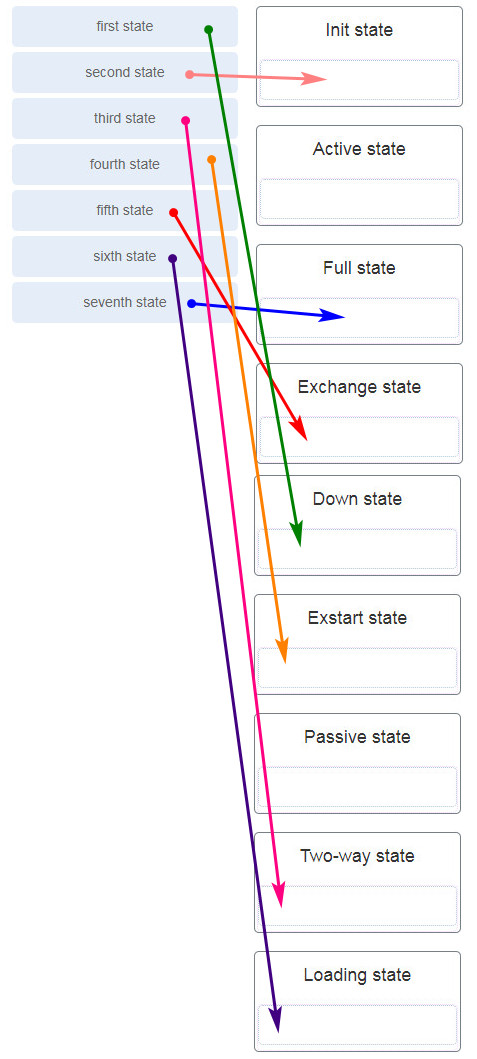
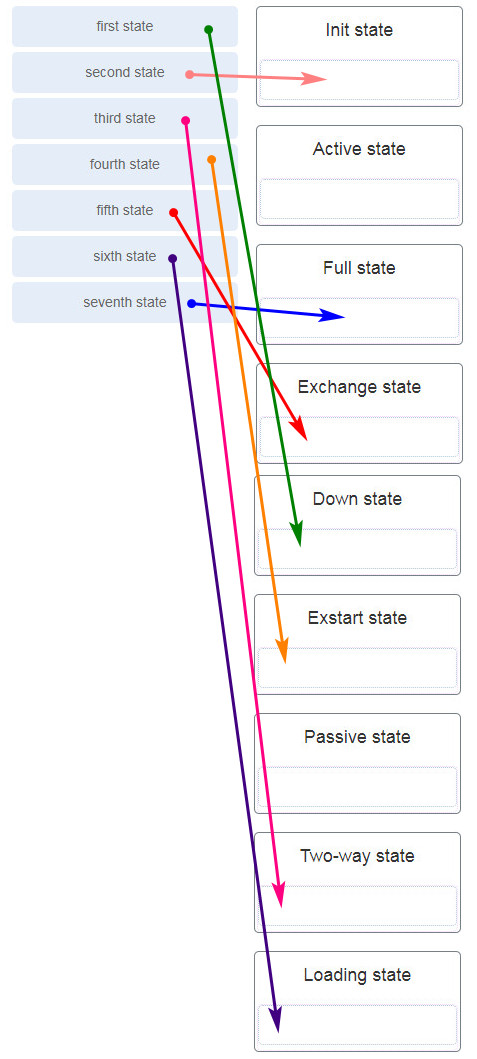
- Disable queuing mechanisms.
- Drop lower-priority packets.
- Prevent bursts of traffic.
- Increase link capacity.
47. What configuration scenario would offer the most protection to SNMP get and set messages?
- SNMPv2 for in-band management with read-write community strings
- SNMPv1 with out-of-band management in a private subnet
- SNMPv3 configured with the auth security level
- SNMP community strings
48. Refer to the exhibit. The network administrator enters these commands into the R1 router:
R1# copy running-config tftp
Address or name of remote host [ ]?
Address or name of remote host [ ]?
When the router prompts for an address or remote host name, what IP address should the administrator enter at the prompt?
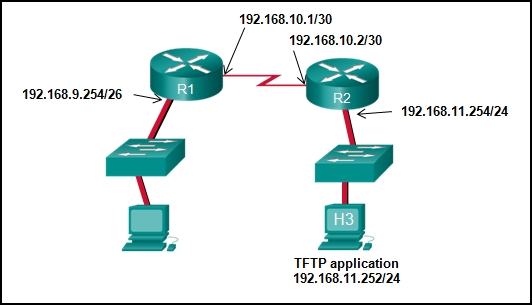
- 192.168.9.254
- 192.168.10.2
- 192.168.11.252
- 192.168.11.254
- 192.168.10.1
49. The command ntp server 10.1.1.1 is issued on a router. What impact does this command have?
- determines which server to send system log files to
- synchronizes the system clock with the time source with IP address 10.1.1.1
- identifies the server on which to store backup configurations
- ensures that all logging will have a time stamp associated with it
50. As the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?
- providing redundant links that dynamically block or forward traffic
- grouping two devices to share a virtual IP address
- grouping multiple physical ports to increase bandwidth between two switches
- providing redundant devices to allow traffic to flow in the event of device failure
51. What is a definition of a two-tier LAN network design?
- access and core layers collapsed into one tier, and the distribution layer on a separate tier
- distribution and core layers collapsed into one tier, and the access layer on a separate tier
- access, distribution, and core layers collapsed into one tier, with a separate backbone layer
- access and distribution layers collapsed into one tier, and the core layer on a separate tier
52. What are two reasons to create a network baseline? (Choose two.)
- to select a routing protocol
- to determine what kind of equipment to implement
- to design a network according to a proper model
- to identify future abnormal network behavior
- to evaluate security vulnerabilities in the network
- to determine if the network can deliver the required policies
53. A computer can access devices on the same network but cannot access devices on other networks. What is the probable cause of this problem?
- The computer has an incorrect subnet mask.
- The computer has an invalid default gateway address.
- The cable is not connected properly to the NIC.
- The computer has an invalid IP address.
54. In which step of gathering symptoms does the network engineer determine if the problem is at the core, distribution, or access layer of the network?
- Gather information.
- Narrow the scope.
- Document the symptoms.
- Determine ownership.
- Determine the symptoms.
55. A network administrator is deploying QoS with the ability to provide a special queue for voice traffic so that voice traffic is forwarded before network traffic in other queues. Which queuing method would be the best choice?
- LLQ
- CBWFQ
- WFQ
- FIFO
56. What are two characteristics of voice traffic? (Choose two.)
- Voice traffic latency should not exceed 150 ms.
- Voice traffic is unpredictable and inconsistent.
- Voice traffic requires at least 384 kbs of bandwidth.
- Voice traffic consumes lots of network resources.
- Dropped voice packets are not retransmitted.
57. Which type of network traffic cannot be managed using congestion avoidance tools?
- TCP
- ICMP
- IP
- UDP
58. When QoS is implemented in a converged network, which two factors can be controlled to improve network performance for real-time traffic? (Choose two.)
- delay
- packet addressing
- jitter
- packet routing
- link speed
59. An administrator wants to replace the configuration file on a Cisco router by loading a new configuration file from a TFTP server. What two things does the administrator need to know before performing this task? (Choose two.)
- name of the configuration file that is currently stored on the router
- configuration register value
- name of the configuration file that is stored on the TFTP server
- router IP address
- TFTP server IP address
60. Refer to the exhibit. Which of the three Cisco IOS images shown will load into RAM?
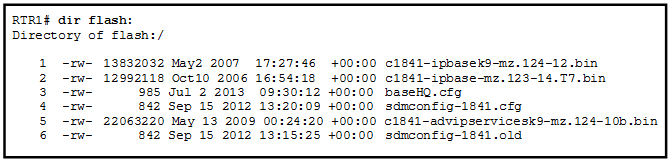
- The router selects an image depending on the boot system command in the configuration.
- The router selects an image depending on the value of the configuration register.
- The router selects the third Cisco IOS image because it is the most recent IOS image.
- The router selects the third Cisco IOS image because it contains the advipservicesk9 image.
- The router selects the second Cisco IOS image because it is the smallest IOS image.
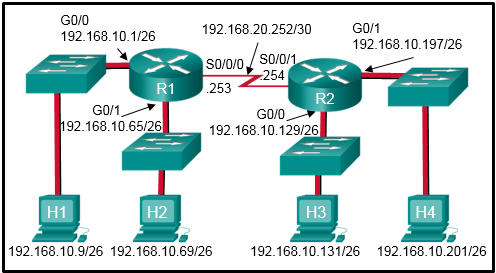
61. Refer to the exhibit. What two types of devices are connected to R1? (Choose two.)
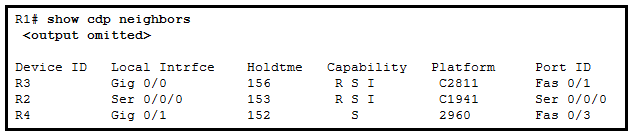
- switch
- hub
- router
- repeater
- Source Route Bridge
62. What are three functions provided by the syslog service? (Choose three.)
- to select the type of logging information that is captured
- to periodically poll agents for data
- to provide statistics on packets that are flowing through a Cisco device
- to provide traffic analysis
- to gather logging information for monitoring and troubleshooting
- to specify the destinations of captured messages
63. What is the function of the MIB element as part of a network management system?
- to collect data from SNMP agents
- to send and retrieve network management information
- to change configurations on SNMP agents
- to store data about a device
64. What network design would contain the scope of disruptions on a network should a failure occur?
- the reduction in the number of redundant devices and connections in the network core
- the installation of only enterprise class equipment throughout the network
- the deployment of distribution layer switches in pairs and the division of access layer switch connections between them
- the configuration of all access layer devices to share a single gateway
65. Which action should be taken when planning for redundancy on a hierarchical network design?
- add alternate physical paths for data to traverse the network
- continually purchase backup equipment for the network
- implement STP portfast between the switches on the network
- immediately replace a non-functioning module, service or device on a network
66. What are two benefits of extending access layer connectivity to users through a wireless medium? (Choose two.)
- increased flexibility
- increased network management options
- decreased number of critical points of failure
- reduced costs
- increased bandwidth availability
67. What is a basic function of the Cisco Borderless Architecture access layer?
- aggregates Layer 2 broadcast domains
- provides access to the user
- aggregates Layer 3 routing boundaries
- provides fault isolation
68. Which characteristic would most influence a network design engineer to select a multilayer switch over a Layer 2 switch?
- ability to have multiple forwarding paths through the switched network based on VLAN number(s)
- ability to build a routing table
- ability to provide power to directly-attached devices and the switch itself
- ability to aggregate multiple ports for maximum data throughput
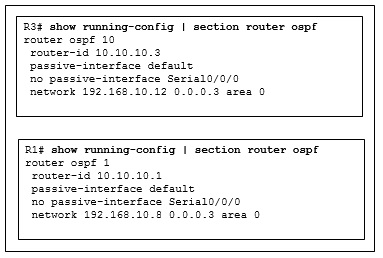
69. Refer to the exhibit. Why are routers R1 and R2 not able to establish an OSPF adjacency?
- The serial interfaces are not in the same area.
- The process numbers are not the same in both routers.
- A backbone router cannot establish an adjacency with an ABR router.
- The router ID values are not the same in both routers.
70. When is the most appropriate time to measure network operations to establish a network performance baseline?
- whenever high network use is detected, so that how the network performs under stress can be monitored
- during quiet vacation periods, so that the level of non-data traffic can be determined
- at the same time each day across a set period of average working days, so that typical traffic patterns can be established
- at random times during a 10 week period, so that abnormal traffic levels can be detected
71. Refer to the exhibit. A user has configured a NIC on the PC as shown but finds that the PC is unable to access the Internet. What is the problem?
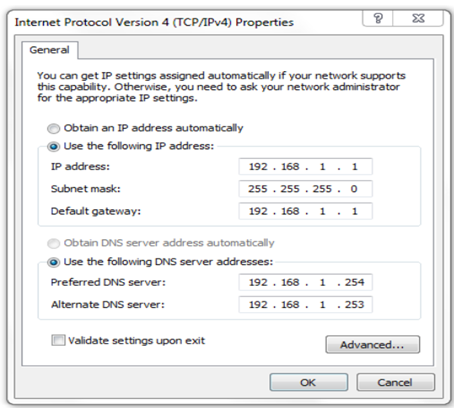
- The preferred DNS address is incorrect.
- The default gateway address is incorrect.
- The settings were not validated upon exit.
- There should not be an alternate DNS server.
72. Refer to the exhibit. A network engineer configured an ACL preventing Telnet and HTTP access to the HQ web server from guest users in the Branch LAN. The address of the web server is 192.168.1.10 and all guest users are assigned addresses in the 192.168.10.0/24 network. After implementing the ACL, no one can access any of the HQ servers. What is the problem?
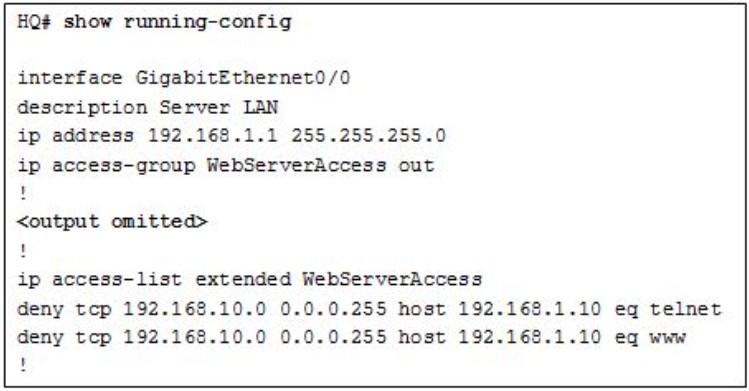
- Inbound ACLs must be routed before they are processed.
- The ACL is implicitly denying access to all the servers.
- Named ACLs require the use of port numbers.
- The ACL is applied to the interface using the wrong direction.
73. Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers as shown. PC1 is unable to connect to PC2. What should the administrator do first when troubleshooting the OSPFv2 implementation?
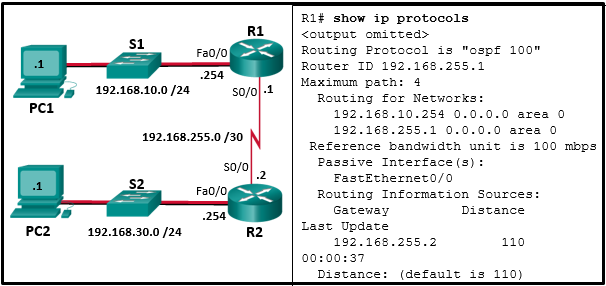
- Disconnect the serial link between router R1 and R2.
- Turn off OSPFv2.
- Implement the network 192.168.255.0 0.0.0.3 area 0 command on router R1.
- Test Layer 3 connectivity between the directly connected routers.
74. What type of traffic is described as requiring latency to be no more than 150 milliseconds (ms)?
- voice
- video
- data
75. A network manager wants to add a time to log messages so that there is record of when the message was generated. What command should the administrator use on a Cisco router?
- show cdp interface
- ntp server 10.10.14.9
- service timestamps log datetime
- clock timezone PST -7
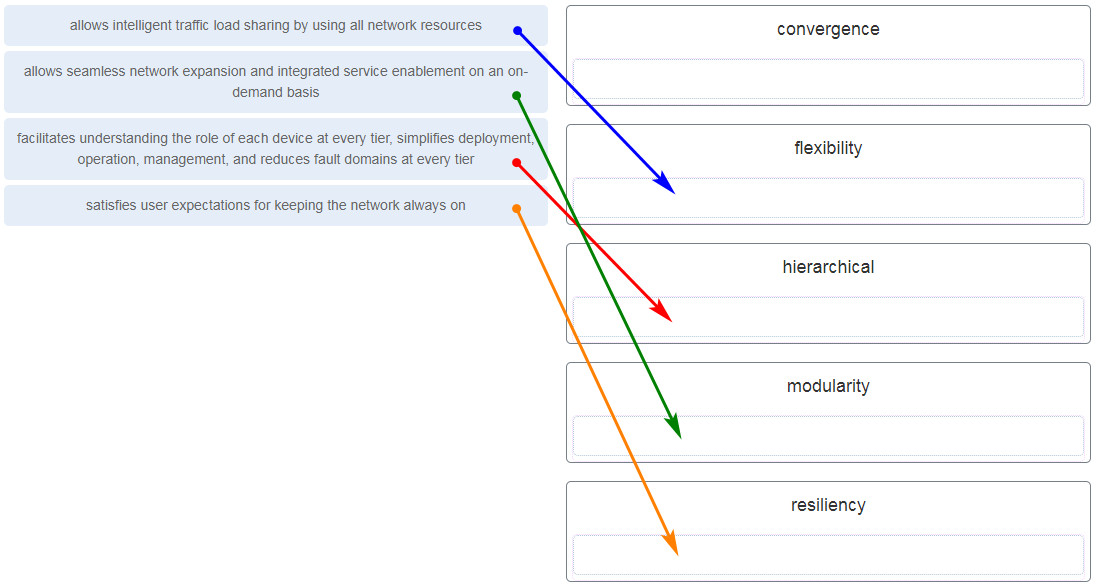
76. Match the functions to the corresponding layers. (Not all options are used.)
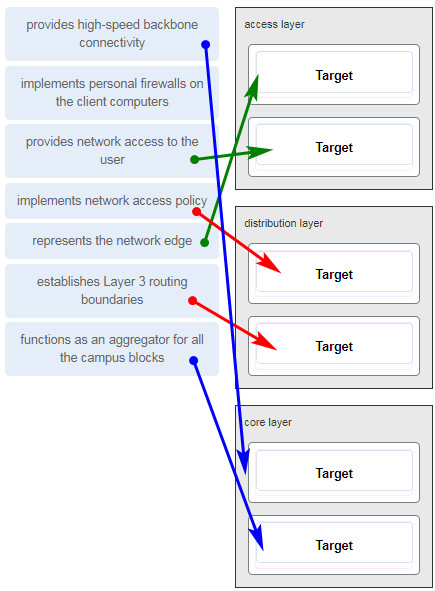
77. Match the borderless switched network guideline description to the principle. (Not all options are used.)
78. What are two characteristics of the best-effort QoS model? (Choose two.)
- It allows end hosts to signal their QoS needs to the network.
- It uses a connection-oriented approach with QoS.
- It provides preferential treatment for voice packets.
- It does not provide a delivery guarantee for packets.
- It treats all network packets in the same way.
79. Why is QoS an important issue in a converged network that combines voice, video, and data communications?
- Data communications are sensitive to jitter.
- Legacy equipment is unable to transmit voice and video without QoS.
Correct Response - Voice and video communications are more sensitive to latency.
- Data communications must be given the first priority.
80. A network administrator configures a router with the command sequence:
R1(config)# boot system tftp://c1900-universalk9-mz.SPA.152-4.M3.bin R1(config)# boot system rom
What is the effect of the command sequence?
- On next reboot, the router will load the IOS image from ROM.
- The router will search and load a valid IOS image in the sequence of flash, TFTP, and ROM.
- The router will copy the IOS image from the TFTP server and then reboot the system.
- The router will load IOS from the TFTP server. If the image fails to load, it will load the IOS image from ROM.
81. Which statement describes SNMP operation?
- An SNMP agent that resides on a managed device collects information about the device and stores that information remotely in the MIB that is located on the NMS.
- A set request is used by the NMS to change configuration variables in the agent device.
- An NMS periodically polls the SNMP agents that are residing on managed devices by using traps to query the devices for data.
- A get request is used by the SNMP agent to query the device for data.
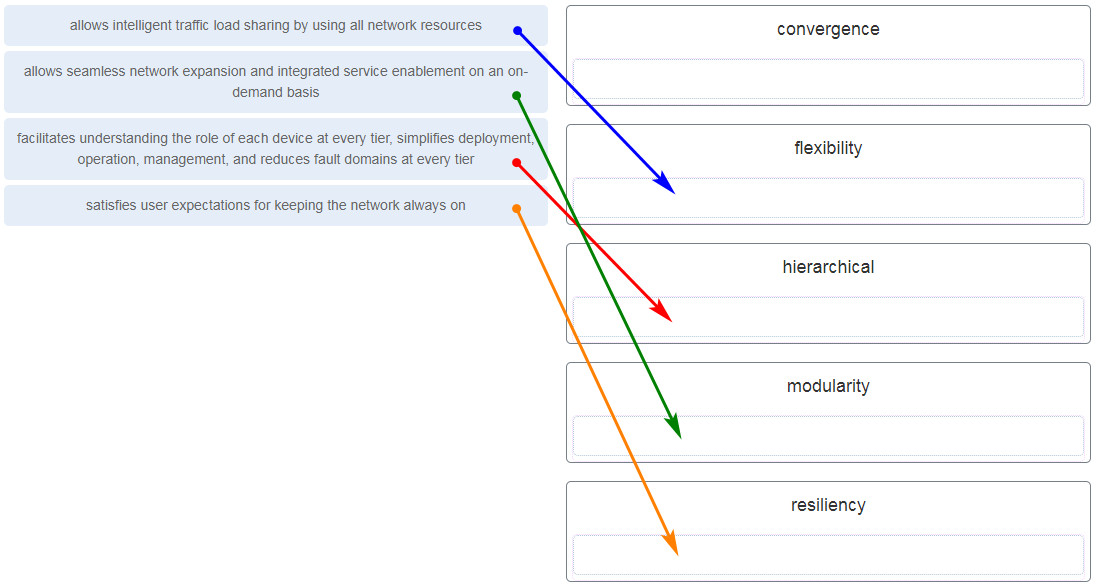
82. Refer to the exhibit. A network administrator issues the show lldp neighbors command on a switch. What are two conclusions that can be drawn? (Choose two.)
- Dev1 is connected to interface Fa0/5 of S1.
- Dev1 is a switch with mixed types of interfaces.
- Dev2 is a switch.
- Dev1 is connected to interface Fa0/4 of Dev2.
- S1 has only two interfaces.
83. What are the three layers of the switch hierarchical design model? (Choose three.)
- distribution
- network access
- data link
- enterprise
- access
- core
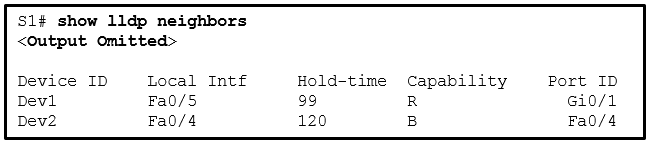
84. Refer to the exhibit. Which devices exist in the failure domain when switch S3 loses power?
- S4 and PC_2
- PC_3 and PC_2
- PC_3 and AP_2
- S1 and S4
- AP_2 and AP_1
85. A network designer is considering whether to implement a switch block on the company network. What is the primary advantage of deploying a switch block?
- This is network application software that prevents the failure of a single network device.
- The failure of a switch block will not impact all end users.
- This is a security feature that is available on all new Catalyst switches.
- A single core router provides all the routing between VLANs.
86. Which troubleshooting tool would a network administrator use to check the Layer 2 header of frames that are leaving a particular host?
- knowledge base
- protocol analyzer
- CiscoView
- baselining tool
87. Refer to the exhibit. R1 and R3 are connected to each other via the local serial 0/0/0 interface. Why are they not forming an adjacency?
- They have different routing processes.
- They have different router IDs.
- They are in different subnets.
- The connecting interfaces are configured as passive.
88. What type of traffic is described as not resilient to loss?
- data
- video
- voice
89. A network manager wants lists the contents of flash. What command should the administrator use on a Cisco router?
- show file systems
- dir
- lldp enable
- service timestamps log datetime
90. Which two statements accurately describe an advantage or a disadvantage when deploying NAT for IPv4 in a network? (Choose two.)
- NAT improves packet handling.
- NAT adds authentication capability to IPv4.
- NAT will impact negatively on switch performance.
- NAT causes routing tables to include more information.
- NAT provides a solution to slow down the IPv4 address depletion.
- NAT introduces problems for some applications that require end-to-end connectivity.
91. A network administrator wants to examine the active NAT translations on a border router. Which command would perform the task?
- Router# show ip nat translations
- Router# show ip nat statistics
- Router# clear ip nat translations
- Router# debug ip nat translations
92. What are two tasks to perform when configuring static NAT? (Choose two.)
- Configure a NAT pool.
- Create a mapping between the inside local and outside local addresses.
- Identify the participating interfaces as inside or outside interfaces.
- Define the inside global address on the server
- Define the outside global address.
93. What is a disadvantage of NAT?
- There is no end-to-end addressing.
- The router does not need to alter the checksum of the IPv4 packets.
- The internal hosts have to use a single public IPv4 address for external communication.
- The costs of readdressing hosts can be significant for a publicly addressed network.
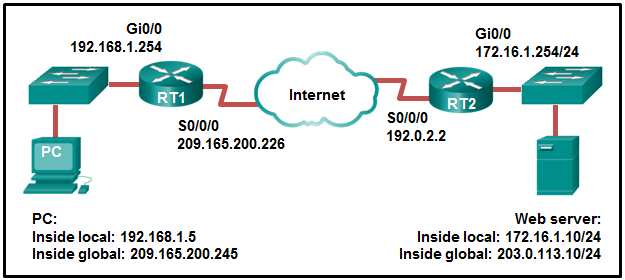
94. Refer to the exhibit. From the perspective of R1, the NAT router, which address is the inside global address?
- 192.168.0.10
- 192.168.0.1
- 209.165.200.225
- 209.165.200.254
95. Refer to the exhibit. Given the commands as shown, how many hosts on the internal LAN off R1 can have simultaneous NAT translations on R1?
- 244
- 10
- 1
- 255
96. Refer to the exhibit. A network administrator has just configured address translation and is verifying the configuration. What three things can the administrator verify? (Choose three.)
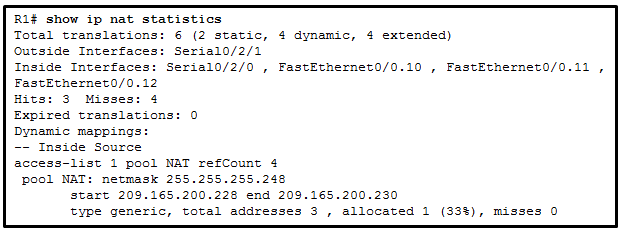
- A standard access list numbered 1 was used as part of the configuration process.
- Three addresses from the NAT pool are being used by hosts.
- Address translation is working.
- One port on the router is not participating in the address translation.
- The name of the NAT pool is refCount.
- Two types of NAT are enabled.
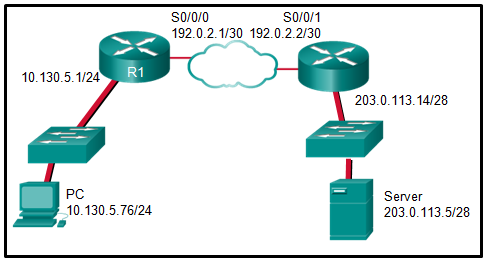
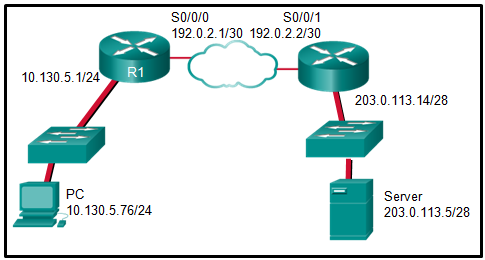
97. Refer to the exhibit. NAT is configured on RT1 and RT2. The PC is sending a request to the web server. What IPv4 address is the source IP address in the packet between RT2 and the web server?
- 192.168.1.5
- 203.0.113.10
- 172.16.1.254
- 172.16.1.10
- 209.165.200.245
- 192.0.2.2
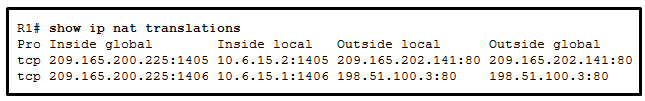
98. Refer to the exhibit. Based on the output that is shown, what type of NAT has been implemented?
- dynamic NAT with a pool of two public IP addresses
- PAT using an external interface
- static NAT with a NAT pool
- static NAT with one entry
99. Refer to the exhibit. From the perspective of users behind the NAT router, what type of NAT address is 209.165.201.1?
- inside global
- outside global
- outside local
- inside local
100. Refer to the exhibit. Static NAT is being configured to allow PC 1 access to the web server on the internal network. What two addresses are needed in place of A and B to complete the static NAT configuration? (Choose two.)
- A = 209.165.201.2
- A = 10.1.0.13
- B = 209.165.201.7
- B = 10.0.254.5
- B = 209.165.201.1
101. What is the purpose of the overload keyword in the ip nat inside source list 1 pool NAT_POOL overload command?
- It allows many inside hosts to share one or a few inside global addresses.
- It allows a list of internal hosts to communicate with a specific group of external hosts.
- It allows external hosts to initiate sessions with internal hosts.
- It allows a pool of inside global addresses to be used by internal hosts.
102. Refer to the exhibit. Which source address is being used by router R1 for packets being forwarded to the Internet?
- 10.6.15.2
- 209.165.202.141
- 198.51.100.3
- 209.165.200.225
103. Refer to the exhibit. The NAT configuration applied to the router is as follows:
ERtr(config)# access-list 1 permit 10.0.0.0 0.255.255.255 ERtr(config)# ip nat pool corp 209.165.201.6 209.165.201.30 netmask 255.255.255.224 ERtr(config)# ip nat inside source list 1 pool corp overload ERtr(config)# ip nat inside source static 10.10.10.55 209.165.201.4 ERtr(config)# interface gigabitethernet 0/0 ERtr(config-if)# ip nat inside ERtr(config-if)# interface serial 0/0/0 ERtr(config-if)# ip nat outside
Based on the configuration and the output shown, what can be determined about the NAT status within the organization?
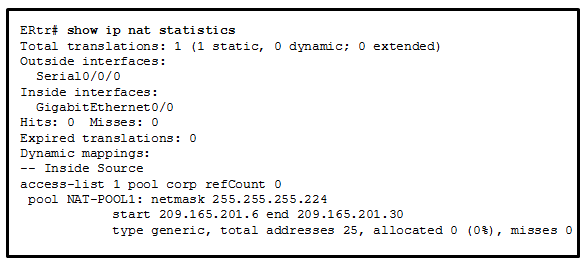
- Static NAT is working, but dynamic NAT is not.
- Dynamic NAT is working, but static NAT is not.
- Not enough information is given to determine if both static and dynamic NAT are working.
- NAT is working.
104. Which situation describes data transmissions over a WAN connection?
- A network administrator in the office remotely accesses a web server that is located in the data center at the edge of the campus.
- A manager sends an email to all employees in the department with offices that are located in several buildings.
- An employee prints a file through a networked printer that is located in another building.
- An employee shares a database file with a co-worker who is located in a branch office on the other side of the city.
105. Which two technologies are categorized as private WAN infrastructures? (Choose two.)
- Frame Relay
- VPN
- MetroE
- DSL
- cable
106. Which network scenario will require the use of a WAN?
- Employees need to connect to the corporate email server through a VPN while traveling.
- Employees need to access web pages that are hosted on the corporate web servers in the DMZ within their building.
- Employee workstations need to obtain dynamically assigned IP addresses.
- Employees in the branch office need to share files with the headquarters office that is located in a separate building on the same campus network.
107. What are two hashing algorithms used with IPsec AH to guarantee authenticity? (Choose two.)
- SHA
- RSA
- DH
- MD5
- AES
108. What two algorithms can be part of an IPsec policy to provide encryption and hashing to protect interesting traffic? (Choose two.)
- SHA
- RSA
- AES
- DH
- PSK
109. Which VPN solution allows the use of a web browser to establish a secure, remote-access VPN tunnel to the ASA?
- client-based SSL
- site-to-site using an ACL
- clientless SSL
- site-to-site using a preshared key
110. Which IPsec security function provides assurance that the data received via a VPN has not been modified in transit?
- integrity
- authentication
- confidentiality
- secure key exchange
111. Which two types of VPNs are examples of enterprise-managed remote access VPNs? (Choose two.)
- clientless SSL VPN
- client-based IPsec VPN
- IPsec VPN
- IPsec Virtual Tunnel Interface VPN
- GRE over IPsec VPN
112. Which is a requirement of a site-to-site VPN?
- It requires hosts to use VPN client software to encapsulate traffic.
- It requires the placement of a VPN server at the edge of the company network.
- It requires a VPN gateway at each end of the tunnel to encrypt and decrypt traffic.
- It requires a client/server architecture.
113. What is the function of the Diffie-Hellman algorithm within the IPsec framework?
- guarantees message integrity
- allows peers to exchange shared keys
- provides authentication
- provides strong data encryption
114. What does NAT overloading use to track multiple internal hosts that use one inside global address?
- port numbers
- IP addresses
- autonomous system numbers
- MAC addresses
115. Question as presented:
116. Refer to the exhibit. R1 is configured for static NAT. What IP address will Internet hosts use to reach PC1?
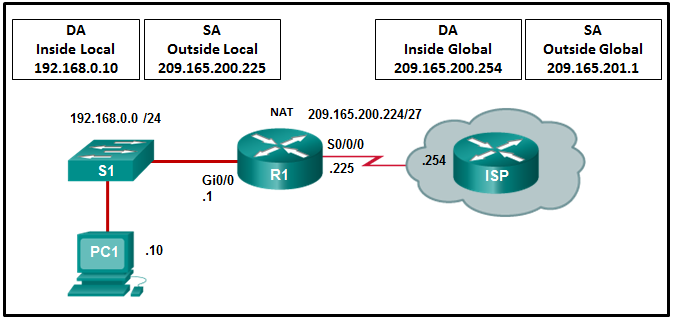
- 192.168.0.1
- 192.168.0.10
- 209.165.201.1
- 209.165.200.225
117. Refer to the exhibit. A network administrator is viewing the output from the command show ip nat translations. Which statement correctly describes the NAT translation that is occurring on router RT2?
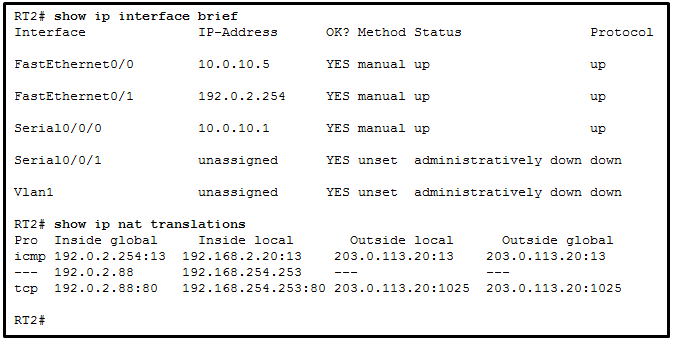
- The traffic from a source IPv4 address of 192.168.254.253 is being translated to 192.0.2.88 by means of static NAT.
- The traffic from a source IPv4 address of 192.0.2.88 is being translated by router RT2 to reach a destination IPv4 address of 192.168.254.253.
- The traffic from a source IPv4 public address that originates traffic on the internet would be able to reach private internal IPv4 addresses.
- The traffic from a source IPv4 address of 192.168.2.20 is being translated by router RT2 to reach a destination IPv4 address of 192.0.2.254.
118. Which two WAN infrastructure services are examples of private connections? (Choose two.)
- cable
- DSL
- Frame Relay
- T1/E1
- wireless
119. Which two statements about the relationship between LANs and WANs are true? (Choose two.)
- Both LANs and WANs connect end devices.
- WANs are typically operated through multiple ISPs, but LANs are typically operated by single organizations or individuals.
- WANs must be publicly-owned, but LANs can be owned by either public or private entities.
- WANs connect LANs at slower speed bandwidth than LANs connect their internal end devices.
- LANs connect multiple WANs together.
120. Which statement describes an important characteristic of a site-to-site VPN?
- It must be statically set up.
- It is ideally suited for use by mobile workers.
- It requires using a VPN client on the host PC.
- After the initial connection is established, it can dynamically change connection information.
- It is commonly implemented over dialup and cable modem networks.
121. How is “tunneling” accomplished in a VPN?
- New headers from one or more VPN protocols encapsulate the original packets.
- All packets between two hosts are assigned to a single physical medium to ensure that the packets are kept private.
- Packets are disguised to look like other types of traffic so that they will be ignored by potential attackers.
- A dedicated circuit is established between the source and destination devices for the duration of the connection.
122. Which statement describes a VPN?
- VPNs use open source virtualization software to create the tunnel through the Internet.
- VPNs use logical connections to create public networks through the Internet.
- VPNs use dedicated physical connections to transfer data between remote users.
- VPNs use virtual connections to create a private network through a public network.
123. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
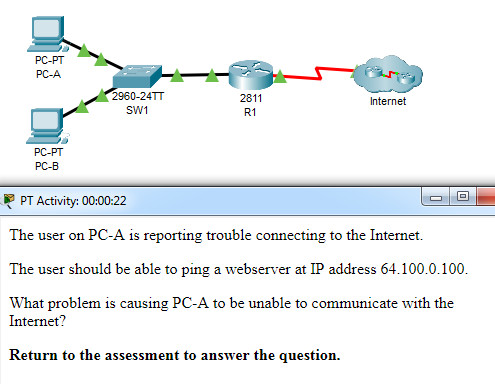
CCNA 3 v7 Modules 6 – 8: WAN Concepts Exam Answers
What problem is causing PC-A to be unable to communicate with the Internet?
- The ip nat inside source command refers to the wrong interface.
- The NAT interfaces are not correctly assigned.
- The static route should not reference the interface, but the outside address instead.
- The access list used in the NAT process is referencing the wrong subnet.
- This router should be configured to use static NAT instead of PAT.
124. What type of address is 64.100.190.189?
- public
- private
125. Which type of VPN routes packets through virtual tunnel interfaces for encryption and forwarding?
- MPLS VPN
- IPsec virtual tunnel interface
- dynamic multipoint VPN
- GRE over IPsec
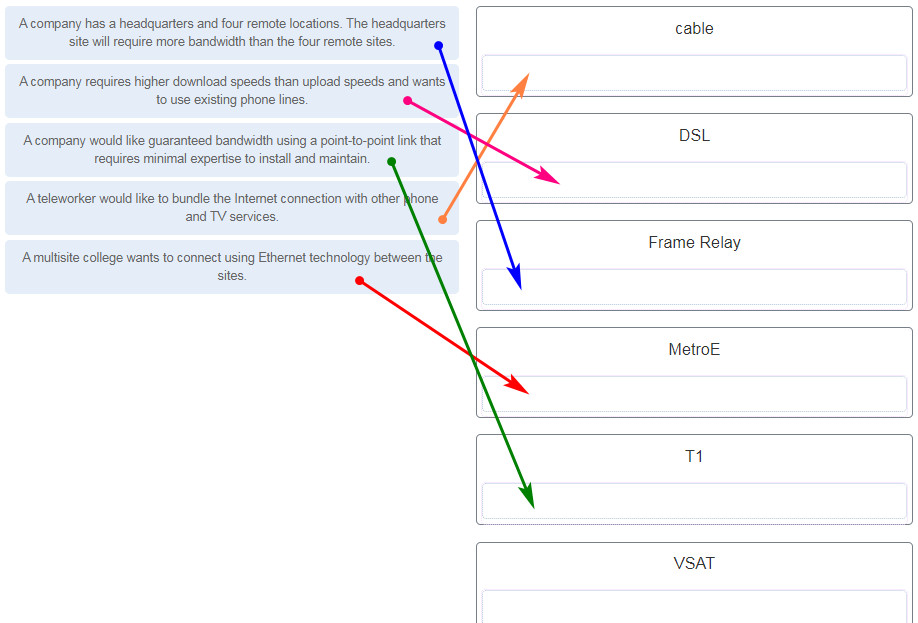
126. Match the scenario to the WAN solution. (Not all options are used.)
127. Question as presented:
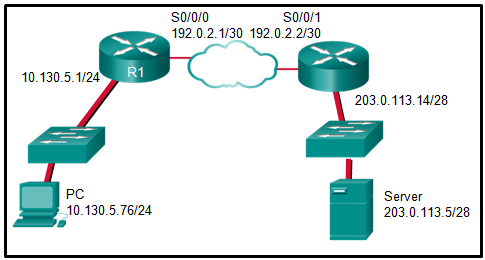
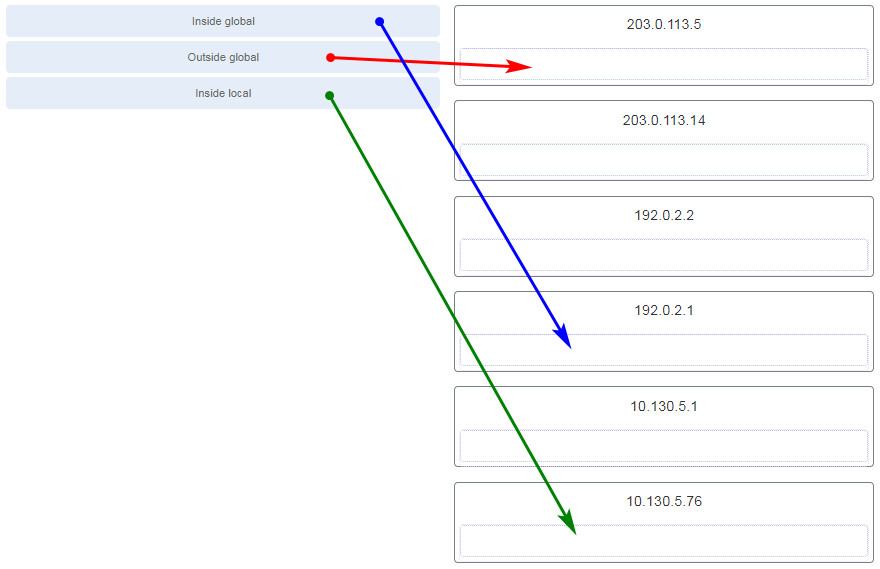
Refer to the exhibit. The PC is sending a packet to the Server on the remote network. Router R1 is performing NAT overload. From the perspective of the PC, match the NAT address type with the correct IP address. (Not all options are used.)
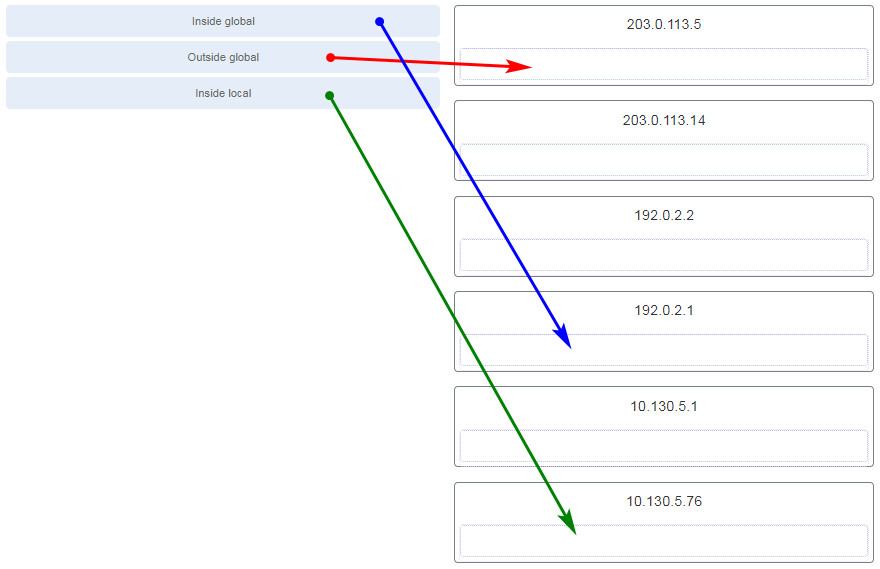
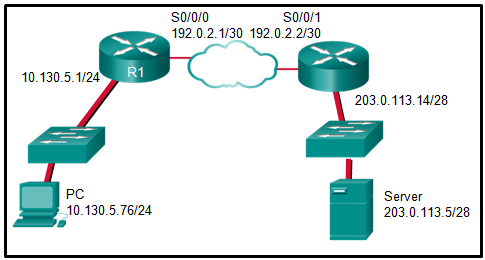
Refer to the exhibit. The PC is sending a packet to the Server on the remote network. Router R1 is performing NAT overload. From the perspective of the PC, match the NAT address type with the correct IP address. (Not all options are used.)
128. Refer to the exhibit. What has to be done in order to complete the static NAT configuration on R1?
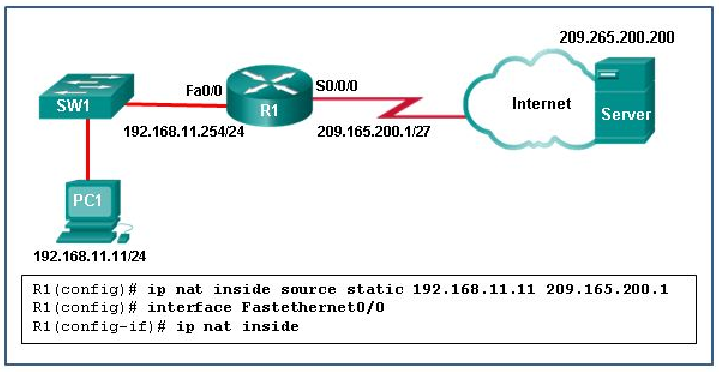
- Interface Fa0/0 should be configured with the command no ip nat inside.
- Interface S0/0/0 should be configured with the command ip nat outside.
- R1 should be configured with the command ip nat inside source static 209.165.200.200 192.168.11.11.
- R1 should be configured with the command ip nat inside source static 209.165.200.1 192.168.11.11.
129. In NAT terms, what address type refers to the globally routable IPv4 address of a destination host on the Internet?
- outside global
- inside global
- outside local
- inside local
130. Refer to the exhibit. Which two statements are correct based on the output as shown in the exhibit? (Choose two.)
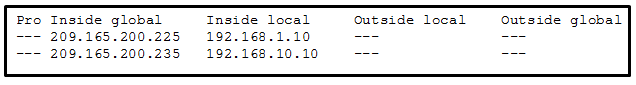
- The output is the result of the show ip nat translations command.
- The host with the address 209.165.200.235 will respond to requests by using a source address of 192.168.10.10.
- The output is the result of the show ip nat statistics command.
- Traffic with the destination address of a public web server will be sourced from the IP of 192.168.1.10.
- The host with the address 209.165.200.235 will respond to requests by using a source address of 209.165.200.235.
131. Which circumstance would result in an enterprise deciding to implement a corporate WAN?
- when the enterprise decides to secure its corporate LAN
- when its employees become distributed across many branch locations
- when the number of employees exceeds the capacity of the LAN
- when the network will span multiple buildings
132. What is the function of the Hashed Message Authentication Code (HMAC) algorithm in setting up an IPsec VPN?
- protects IPsec keys during session negotiation
- authenticates the IPsec peers
- creates a secure channel for key negotiation
- guarantees message integrity
133. What algorithm is used with IPsec to provide data confidentiality?
- Diffie-Hellman
- SHA
- MD5
- RSA
- AES
134. Which two technologies provide enterprise-managed VPN solutions? (Choose two.)
- remote access VPN
- Frame Relay
- Layer 2 MPLS VPN
- site-to-site VPN
- Layer 3 MPLS VPN
135. Question as presented:
136. Refer to the exhibit. A network administrator is viewing the output from the command show ip nat translations. Which statement correctly describes the NAT translation that is occurring on router RT2?
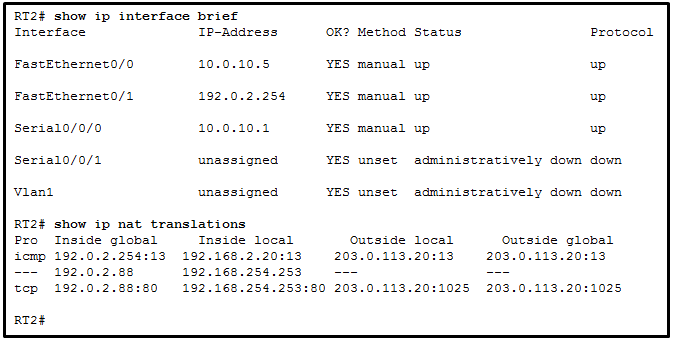
- The traffic from a source IPv4 address of 192.168.254.253 is being translated to 192.0.2.88 by means of static NAT.
- The traffic from a source IPv4 address of 192.0.2.88 is being translated by router RT2 to reach a destination IPv4 address of 192.168.254.253.
- The traffic from a source IPv4 public address that originates traffic on the internet would be able to reach private internal IPv4 addresses.
- The traffic from a source IPv4 address of 192.168.2.20 is being translated by router RT2 to reach a destination IPv4 address of 192.0.2.254.
137. What type of address is 10.100.126.126?
- private
- public
138. Which type of VPN connects using the Transport Layer Security (TLS) feature?
- SSL VPN
- MPLS VPN
- IPsec virtual tunnel interface
- dynamic multipoint VPN
139. The IT department is reporting that a company web server is receiving an abnormally high number of web page requests from different locations simultaneously. Which type of security attack is occurring?
- adware
- DDoS
- phishing
- social engineering
- spyware
140. What causes a buffer overflow?
- launching a security countermeasure to mitigate a Trojan horse
- downloading and installing too many software updates at one time
- attempting to write more data to a memory location than that location can hold
- sending too much information to two or more interfaces of the same device, thereby causing dropped packets
- sending repeated connections such as Telnet to a particular device, thus denying other data sources
141. Which objective of secure communications is achieved by encrypting data?
- authentication
- availability
- confidentiality
- integrity
142. What type of malware has the primary objective of spreading across the network?
- worm
- virus
- Trojan horse
- botnet
143. What commonly motivates cybercriminals to attack networks as compared to hactivists or state-sponsored hackers?
- financial gain
- fame seeking
- status among peers
- political reasons
144. Which type of hacker is motivated to protest against political and social issues?
- hacktivist
- cybercriminal
- script kiddie
- vulnerability broker
145. What is a ping sweep?
- a query and response protocol that identifies information about a domain, including the addresses that are assigned to that domain.
- a scanning technique that examines a range of TCP or UDP port numbers on a host to detect listening services.
- a software application that enables the capture of all network packets that are sent across a LAN.
- a network scanning technique that indicates the live hosts in a range of IP addresses.
146. In what type of attack is a cybercriminal attempting to prevent legitimate users from accessing network services?
- address spoofing
- MITM
- session hijacking
- DoS
147. Which requirement of secure communications is ensured by the implementation of MD5 or SHA hash generating algorithms?
- nonrepudiation
- authentication
- integrity
- confidentiality
148. If an asymmetric algorithm uses a public key to encrypt data, what is used to decrypt it?
- a digital certificate
- a different public key
- a private key
- DH
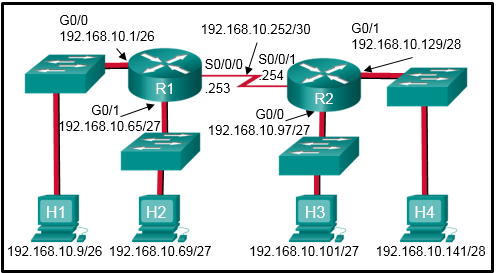
149. Refer to the exhibit. Which two ACLs would permit only the two LAN networks attached to R1 to access the network that connects to R2 G0/1 interface? (Choose two.)
- access-list 1 permit 192.168.10.0 0.0.0.127
- access-list 2 permit host 192.168.10.9
access-list 2 permit host 192.168.10.69 - access-list 5 permit 192.168.10.0 0.0.0.63
access-list 5 permit 192.168.10.64 0.0.0.63 - access-list 3 permit 192.168.10.128 0.0.0.63
- access-list 4 permit 192.168.10.0 0.0.0.255
150. Which two packet filters could a network administrator use on an IPv4 extended ACL? (Choose two.)
- destination UDP port number
- computer type
- destination MAC address
- ICMP message type
- source TCP hello address
151. What type of ACL offers greater flexibility and control over network access?
- numbered standard
- named standard
- extended
- flexible
152. What is the quickest way to remove a single ACE from a named ACL?
- Use the no keyword and the sequence number of the ACE to be removed.
- Copy the ACL into a text editor, remove the ACE, then copy the ACL back into the router.
- Create a new ACL with a different number and apply the new ACL to the router interface.
- Use the no access-list command to remove the entire ACL, then recreate it without the ACE.
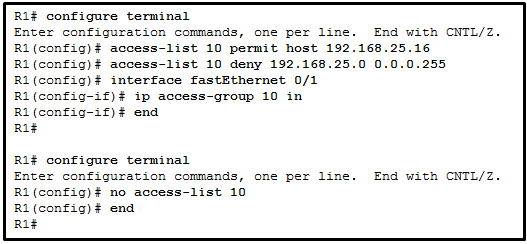
153. Refer to the exhibit. A network administrator is configuring a standard IPv4 ACL. What is the effect after the command no access-list 10 is entered?
- ACL 10 is removed from both the running configuration and the interface Fa0/1.
- ACL 10 is removed from the running configuration.
- ACL 10 is disabled on Fa0/1.
- ACL 10 will be disabled and removed after R1 restarts.
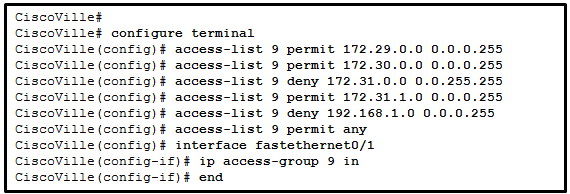
154. Refer to the exhibit. A network administrator has configured ACL 9 as shown. Users on the 172.31.1.0 /24 network cannot forward traffic through router CiscoVille. What is the most likely cause of the traffic failure?
- The established keyword is not specified.
- The sequence of the ACEs is incorrect.
- The port number for the traffic has not been identified with the eq keyword.
- The permit statement specifies an incorrect wildcard mask.
155. A network administrator needs to configure a standard ACL so that only the workstation of the administrator with the IP address 192.168.15.23 can access the virtual terminal of the main router. Which two configuration commands can achieve the task? (Choose two.)
- Router1(config)# access-list 10 permit 192.168.15.23 0.0.0.0
- Router1(config)# access-list 10 permit 192.168.15.23 0.0.0.255
- Router1(config)# access-list 10 permit 192.168.15.23 255.255.255.255
- Router1(config)# access-list 10 permit host 192.168.15.23
- Router1(config)# access-list 10 permit 192.168.15.23 255.255.255.0
156. Refer to the exhibit. Which command would be used in a standard ACL to allow only devices on the network attached to R2 G0/0 interface to access the networks attached to R1?
- access-list 1 permit 192.168.10.128 0.0.0.63
- access-list 1 permit 192.168.10.0 0.0.0.255
- access-list 1 permit 192.168.10.96 0.0.0.31
- access-list 1 permit 192.168.10.0 0.0.0.63
157. A network administrator is writing a standard ACL that will deny any traffic from the 172.16.0.0/16 network, but permit all other traffic. Which two commands should be used? (Choose two.)
- Router(config)# access-list 95 deny 172.16.0.0 255.255.0.0
- Router(config)# access-list 95 permit any
- Router(config)# access-list 95 host 172.16.0.0
- Router(config)# access-list 95 deny 172.16.0.0 0.0.255.255
- Router(config)# access-list 95 172.16.0.0 255.255.255.255
- Router(config)# access-list 95 deny any
158. Refer to the exhibit. An ACL was configured on R1 with the intention of denying traffic from subnet 172.16.4.0/24 into subnet 172.16.3.0/24. All other traffic into subnet 172.16.3.0/24 should be permitted. This standard ACL was then applied outbound on interface Fa0/0. Which conclusion can be drawn from this configuration?
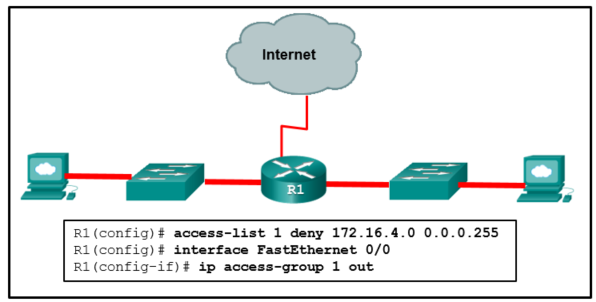
- The ACL should be applied outbound on all interfaces of R1.
- The ACL should be applied to the FastEthernet 0/0 interface of R1 inbound to accomplish the requirements.
- All traffic will be blocked, not just traffic from the 172.16.4.0/24 subnet.
- Only traffic from the 172.16.4.0/24 subnet is blocked, and all other traffic is allowed.
- An extended ACL must be used in this situation.
159. Refer to the exhibit. A network administrator needs to add an ACE to the TRAFFIC-CONTROL ACL that will deny IP traffic from the subnet 172.23.16.0/20. Which ACE will meet this requirement?
- 30 deny 172.23.16.0 0.0.15.255
- 15 deny 172.23.16.0 0.0.15.255
- 5 deny 172.23.16.0 0.0.15.255
- 5 deny 172.23.16.0 0.0.255.255
160. Refer to the exhibit. A network administrator configures an ACL on the router. Which statement describes the result of the configuration?
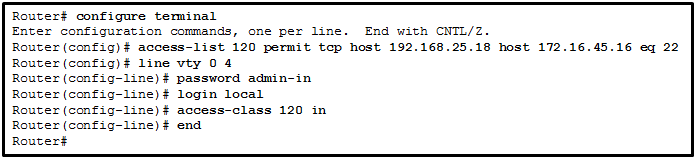
- An SSH connection is allowed from a workstation with IP 172.16.45.16 to a device with IP 192.168.25.18.
- An SSH connection is allowed from a workstation with IP 192.168.25.18 to a device with IP 172.16.45.16.
- A Telnet connection is allowed from a workstation with IP 192.168.25.18 to a device with IP 172.16.45.16.
- A Telnet connection is allowed from a workstation with IP 172.16.45.16 to a device with IP 192.168.25.18.
161. Refer to the exhibit. What can be determined from this output?
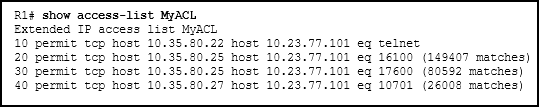
- The ACL is missing the deny ip any any ACE.
- The ACL is only monitoring traffic destined for 10.23.77.101 from three specific hosts.
- Because there are no matches for line 10, the ACL is not working.
- The router has not had any Telnet packets from 10.35.80.22 that are destined for 10.23.77.101.
162. Refer to the exhibit. A network administrator wants to permit only host 192.168.1.1 /24 to be able to access the server 192.168.2.1 /24. Which three commands will achieve this using best ACL placement practices? (Choose three.)
- R2(config)# interface fastethernet 0/1
- R2(config-if)# ip access-group 101 out
- R2(config)# access-list 101 permit ip 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
- R2(config-if)# ip access-group 101 in
- R2(config)# access-list 101 permit ip any any
- R2(config)# interface fastethernet 0/0
- R2(config)# access-list 101 permit ip host 192.168.1.1 host 192.168.2.1
163. Consider the following access list.
access-list 100 permit ip host 192.168.10.1 any
access-list 100 deny icmp 192.168.10.0 0.0.0.255 any echo
access-list 100 permit ip any any
access-list 100 deny icmp 192.168.10.0 0.0.0.255 any echo
access-list 100 permit ip any any
Which two actions are taken if the access list is placed inbound on a router Gigabit Ethernet port that has the IP address 192.168.10.254 assigned? (Choose two.)
- Only Layer 3 connections are allowed to be made from the router to any other network device.
- Devices on the 192.168.10.0/24 network are not allowed to reply to any ping requests.
- Devices on the 192.168.10.0/24 network can sucessfully ping devices on the 192.168.11.0 network.
- A Telnet or SSH session is allowed from any device on the 192.168.10.0 into the router with this access list assigned.
- Only the network device assigned the IP address 192.168.10.1 is allowed to access the router.
164. Refer to the exhibit. The named ACL “Managers” already exists on the router. What will happen when the network administrator issues the commands that are shown in the exhibit?
- The commands are added at the end of the existing Managers ACL.
- The commands overwrite the existing Managers ACL.
- The commands are added at the beginning of the existing Managers ACL.
- The network administrator receives an error that states that the ACL already exists.
165. In which TCP attack is the cybercriminal attempting to overwhelm a target host with half-open TCP connections?
- port scan attack
- SYN flood attack
- session hijacking attack
- reset attack
166. Which protocol is attacked when a cybercriminal provides an invalid gateway in order to create a man-in-the-middle attack?
- DHCP
- DNS
- ICMP
- HTTP or HTTPS
167. Refer to the exhibit. An administrator has configured a standard ACL on R1 and applied it to interface serial 0/0/0 in the outbound direction. What happens to traffic leaving interface serial 0/0/0 that does not match the configured ACL statements?
- The traffic is dropped.
- The source IP address is checked and, if a match is not found, traffic is routed out interface serial 0/0/1.
- The resulting action is determined by the destination IP address.
- The resulting action is determined by the destination IP address and port number.
168. Refer to the exhibit. The Gigabit interfaces on both routers have been configured with subinterface numbers that match the VLAN numbers connected to them. PCs on VLAN 10 should be able to print to the P1 printer on VLAN 12. PCs on VLAN 20 should print to the printers on VLAN 22. What interface and in what direction should you place a standard ACL that allows printing to P1 from data VLAN 10, but stops the PCs on VLAN 20 from using the P1 printer? (Choose two.)
- inbound
- R2 S0/0/1
- R1 Gi0/1.12
- outbound
- R1 S0/0/0
- R2 Gi0/1.20
169. Which statement describes a characteristic of standard IPv4 ACLs?
- They are configured in the interface configuration mode.
- They can be configured to filter traffic based on both source IP addresses and source ports.
- They can be created with a number but not with a name.
- They filter traffic based on source IP addresses only.
170. What is considered a best practice when configuring ACLs on vty lines?
- Place identical restrictions on all vty lines.
- Remove the vty password since the ACL restricts access to trusted users.
- Apply the ip access-group command inbound.
- Use only extended access lists.
171.
Refer to the exhibit. An administrator first configured an extended ACL as shown by the output of the show access-lists command. The administrator then edited this access-list by issuing the commands below.
Router(config)# ip access-list extended 101 Router(config-ext-nacl)# no 20 Router(config-ext-nacl)# 5 permit tcp any any eq 22 Router(config-ext-nacl)# 20 deny udp any any
Which two conclusions can be drawn from this new configuration? (Choose two.)
- TFTP packets will be permitted.
- Ping packets will be permitted.
- Telnet packets will be permitted.
- SSH packets will be permitted.
- All TCP and UDP packets will be denied.
172. Which set of access control entries would allow all users on the 192.168.10.0/24 network to access a web server that is located at 172.17.80.1, but would not allow them to use Telnet?
- access-list 103 deny tcp host 192.168.10.0 any eq 23
access-list 103 permit tcp host 192.168.10.1 eq 80 - access-list 103 permit tcp 192.168.10.0 0.0.0.255 any eq 80
access-list 103 deny tcp 192.168.10.0 0.0.0.255 any eq 23 - access-list 103 permit 192.168.10.0 0.0.0.255 host 172.17.80.1
access-list 103 deny tcp 192.168.10.0 0.0.0.255 any eq telnet - access-list 103 permit tcp 192.168.10.0 0.0.0.255 host 172.17.80.1 eq 80
access-list 103 deny tcp 192.168.10.0 0.0.0.255 any eq 23
173. What is the term used to describe a mechanism that takes advantage of a vulnerability?
- mitigation
- exploit
- vulnerability
- threat
174. Refer to the exhibit. The network administrator has an IP address of 192.168.11.10 and needs access to manage R1. What is the best ACL type and placement to use in this situation?

- extended ACL outbound on R2 WAN interface towards the internet
- standard ACL inbound on R1 vty lines
- extended ACLs inbound on R1 G0/0 and G0/1
- extended ACL outbound on R2 S0/0/1
175. A technician is tasked with using ACLs to secure a router. When would the technician use the any configuration option or command?
- to add a text entry for documentation purposes
- to generate and send an informational message whenever the ACE is matched
- to identify any IP address
- to identify one specific IP address
176. Which statement accurately characterizes the evolution of threats to network security?
- Internet architects planned for network security from the beginning.
- Early Internet users often engaged in activities that would harm other users.
- Internal threats can cause even greater damage than external threats.
- Threats have become less sophisticated while the technical knowledge needed by an attacker has grown.
177. A user receives a phone call from a person who claims to represent IT services and then asks that user for confirmation of username and password for auditing purposes. Which security threat does this phone call represent?
- spam
- social engineering
- DDoS
- anonymous keylogging
178. In what way are zombies used in security attacks?
- They target specific individuals to gain corporate or personal information.
- They probe a group of machines for open ports to learn which services are running.
- They are maliciously formed code segments used to replace legitimate applications.
- They are infected machines that carry out a DDoS attack.
179. Which attack involves threat actors positioning themselves between a source and destination with the intent of transparently monitoring, capturing, and controlling the communication?
- man-in-the-middle attack
- SYN flood attack
- DoS attack
- ICMP attack
180. Which two keywords can be used in an access control list to replace a wildcard mask or address and wildcard mask pair? (Choose two.)
- host
- most
- gt
- some
- any
- all
181. Refer to the exhibit. The student on the H1 computer continues to launch an extended ping with expanded packets at the student on the H2 computer. The school network administrator wants to stop this behavior, but still allow both students access to web-based computer assignments. What would be the best plan for the network administrator?
CCNA 3 v7 Modules 3 – 5: Network Security Exam Answers 42
- Apply an inbound standard ACL on R1 Gi0/0.
- Apply an inbound extended ACL on R2 Gi0/1.
- Apply an outbound extended ACL on R1 S0/0/1.
- Apply an inbound extended ACL on R1 Gi0/0.
- Apply an outbound standard ACL on R2 S0/0/1.
182. Which statement describes a difference between the operation of inbound and outbound ACLs?
- Inbound ACLs are processed before the packets are routed while outbound ACLs are processed after the routing is completed.
- In contrast to outbound ALCs, inbound ACLs can be used to filter packets with multiple criteria.
- On a network interface, more than one inbound ACL can be configured but only one outbound ACL can be configured.
- Inbound ACLs can be used in both routers and switches but outbound ACLs can be used only on routers.
183. What effect would the Router1(config-ext-nacl)# permit tcp 172.16.4.0 0.0.0.255 any eq www command have when implemented inbound on the f0/0 interface?
- All TCP traffic is permitted, and all other traffic is denied.
- Traffic originating from 172.16.4.0/24 is permitted to all TCP port 80 destinations.
- All traffic from 172.16.4.0/24 is permitted anywhere on any port.
- The command is rejected by the router because it is incomplete.
184. Which ACE will permit a packet that originates from any network and is destined for a web server at 192.168.1.1?
- access-list 101 permit tcp any host 192.168.1.1 eq 80
- access-list 101 permit tcp host 192.168.1.1 eq 80 any
- access-list 101 permit tcp host 192.168.1.1 any eq 80
- access-list 101 permit tcp any eq 80 host 192.168.1.1
185. Refer to the exhibit. A new network policy requires an ACL denying FTP and Telnet access to a Corp file server from all interns. The address of the file server is 172.16.1.15 and all interns are assigned addresses in the 172.18.200.0/24 network. After implementing the ACL, no one in the Corp network can access any of the servers. What is the problem?
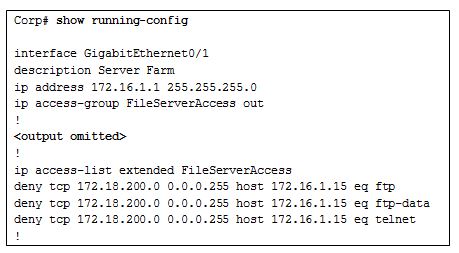
CCNA 3 v7 Modules 3 – 5: Network Security Exam Answers 46
- Inbound ACLs must be routed before they are processed.
- The ACL is implicitly denying access to all the servers.
- Named ACLs require the use of port numbers.
- The ACL is applied to the interface using the wrong direction.
186. A technician is tasked with using ACLs to secure a router. When would the technician use the access-class 20 in configuration option or command?
- to secure administrative access to the router
- to remove an ACL from an interface
- to remove a configured ACL
- to apply a standard ACL to an interface
187. What is the term used to describe the same pre-shared key or secret key, known by both the sender and receiver to encrypt and decrypt data?
- symmetric encryption algorithm
- data integrity
- exploit
- risk
188. Refer to the exhibit. Internet privileges for an employee have been revoked because of abuse but the employee still needs access to company resources. What is the best ACL type and placement to use in this situation?

CCNA 3 v7 Modules 3 – 5: Network Security Exam Answers 49
- standard ACL inbound on R2 WAN interface connecting to the internet
- standard ACL outbound on R2 WAN interface towards the internet
- standard ACL inbound on R1 G0/0
- standard ACL outbound on R1 G0/0
189. What is a function of OSPF hello packets?
- to send specifically requested link-state records
- to discover neighbors and build adjacencies between them
- to ensure database synchronization between routers
- to request specific link-state records from neighbor routers
190. Which OPSF packet contains the different types of link-state advertisements?
- hello
- DBD
- LSR
- LSU
- LSAck
191. Which three statements describe features of the OSPF topology table? (Choose three.)
- It is a link-state database that represents the network topology.
- Its contents are the result of running the SPF algorithm.
- When converged, all routers in an area have identical topology tables.
- The topology table contains feasible successor routes.
- The table can be viewed via the show ip ospf database command.
- After convergence, the table only contains the lowest cost route entries for all known networks.
192. What does an OSPF area contain?
- routers that share the same router ID
- routers whose SPF trees are identical
- routers that have the same link-state information in their LSDBs
- routers that share the same process ID
193. What is used to facilitate hierarchical routing in OSPF?
- the use of multiple areas
- frequent SPF calculations
- autosummarization
- the election of designated routers
194. Which OSPF data structure is identical on all OSPF routers that share the same area?
- forwarding database
- link-state database
- adjacency database
- routing table
195. Which step does an OSPF-enabled router take immediately after establishing an adjacency with another router?
- builds the topology table
- exchanges link-state advertisements
- chooses the best path
- executes the SPF algorithm
196. A network engineer has manually configured the hello interval to 15 seconds on an interface of a router that is running OSPFv2. By default, how will the dead interval on the interface be affected?
- The dead interval will not change from the default value.
- The dead interval will now be 30 seconds.
- The dead interval will now be 60 seconds.
- The dead interval will now be 15 seconds.
197. Refer to the exhibit. A network administrator has configured the OSPF timers to the values that are shown in the graphic. What is the result of having those manually configured timers?
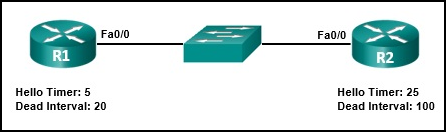
- R1 automatically adjusts its own timers to match the R2 timers.
- The R1 dead timer expires between hello packets from R2.
- The hello timer on R2 expires every ten seconds.
- The neighbor adjacency has formed.
198. To establish a neighbor adjacency two OSPF routers will exchange hello packets. Which two values in the hello packets must match on both routers? (Choose two.)
- dead interval
- router priority
- list of neighbors
- router ID
- hello interval
199. What is the default router priority value for all Cisco OSPF routers?
- 0
- 1
- 10
- 255
200. Which type of OSPFv2 packet contains an abbreviated list of the LSDB of a sending router and is used by receiving routers to check against the local LSDB?
- database description
- link-state update
- link-state request
- link-state acknowledgment
201. In an OSPF network when are DR and BDR elections required?
- when the two adjacent neighbors are interconnected over a point-to-point link
- when all the routers in an OSPF area cannot form adjacencies
- when the routers are interconnected over a common Ethernet network
- when the two adjacent neighbors are in two different networks
202. When an OSPF network is converged and no network topology change has been detected by a router, how often will LSU packets be sent to neighboring routers?
- every 5 minutes
- every 10 minutes
- every 30 minutes
- every 60 minutes
203. What will an OSPF router prefer to use first as a router ID?
- a loopback interface that is configured with the highest IP address on the router
- any IP address that is configured using the router-id command
- the highest active interface IP that is configured on the router
- the highest active interface that participates in the routing process because of a specifically configured network statement
204. What are the two purposes of an OSPF router ID? (Choose two.)
- to uniquely identify the router within the OSPF domain
- to facilitate router participation in the election of the designated router
- to enable the SPF algorithm to determine the lowest cost path to remote networks
- to facilitate the establishment of network convergence
- to facilitate the transition of the OSPF neighbor state to Full
205. Refer to the exhibit. If no router ID was manually configured, what would router Branch1 use as its OSPF router ID?
- 10.0.0.1
- 10.1.0.1
- 192.168.1.100
- 209.165.201.1
206. A network technician issues the following commands when configuring a router:
R1(config)# router ospf 11 R1(config-router)# network 10.10.10.0 0.0.0.255 area 0
What does the number 11 represent?
- the OSPF process ID on R1
- the cost of the link to R1
- the autonomous system number to which R1 belongs
- the administrative distance that is manually assigned to R1
- the area number where R1 is located
207. An OSPF router has three directly connected networks; 172.16.0.0/16, 172.16.1.0/16, and 172.16.2.0/16. Which OSPF network command would advertise only the 172.16.1.0 network to neighbors?
- router(config-router)# network 172.16.1.0 0.0.255.255 area 0
- router(config-router)# network 172.16.0.0 0.0.15.255 area 0
- router(config-router)# network 172.16.1.0 255.255.255.0 area 0
- router(config-router)# network 172.16.1.0 0.0.0.0 area 0
208. Refer to the exhibit. Which three statements describe the results of the OSPF election process of the topology that is shown in the exhibit? (Choose three.)
- R3 will be elected BDR.
- The R4 FastEthernet 0/0 priority is 128.
- The R4 router ID is 172.16.1.1.
- R1 will be elected BDR.
- The router ID on R2 is the loopback interface.
- R2 will be elected DR.
209. Refer to the exhibit. If the switch reboots and all routers have to re-establish OSPF adjacencies, which routers will become the new DR and BDR?
- Router R4 will become the DR and router R1 will become the BDR.
- Router R2 will become the DR and router R3 will become the BDR.
- Router R1 will become the DR and router R2 will become the BDR.
- Router R4 will become the DR and router R3 will become the BDR.
210. By default, what is the OSPF cost for any link with a bandwidth of 100 Mb/s or greater?
- 100000000
- 10000
- 1
- 100
211. Refer to the exhibit. What is the OSPF cost to reach the router A LAN 172.16.1.0/24 from B?
- 782
- 74
- 128
- 65
212. Refer to the exhibit. On which router or routers would a default route be statically configured in a corporate environment that uses single area OSPF as the routing protocol?
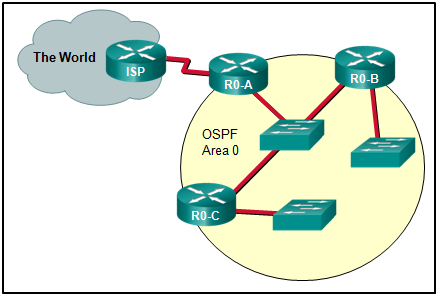
- R0-A
- ISP, R0-A, R0-B, and R0-C
- ISP
- R0-B and R0-C
- ISP and R0-A
- R0-A, R0-B, and R0-C
213. What command would be used to determine if a routing protocol-initiated relationship had been made with an adjacent router?
- ping
- show ip ospf neighbor
- show ip interface brief
- show ip protocols
214. Refer to the exhibit. Which command did an administrator issue to produce this output?
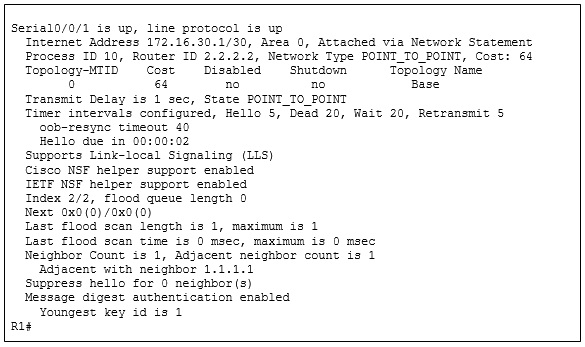
- R1# show ip ospf interface serial0/0/1
- R1# show ip route ospf
- R1# show ip ospf
- R1# show ip ospf neighbor
215. Which command is used to verify that OSPF is enabled and also provides a list of the networks that are being advertised by the network?
- show ip interface brief
- show ip ospf interface
- show ip protocols
- show ip route ospf
216. Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers but PC1 is unable to connect to PC2. What is the most likely problem?
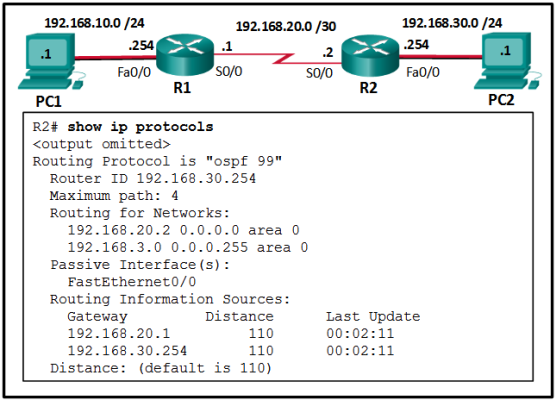
- Interface Fa0/0 has not been activated for OSPFv2 on router R2.
- Interface Fa0/0 is configured as a passive-interface on router R2.
- Interface S0/0 is configured as a passive-interface on router R2.
- Interface s0/0 has not been activated for OSPFv2 on router R2.
217. What is the recommended Cisco best practice for configuring an OSPF-enabled router so that each router can be easily identified when troubleshooting routing issues?
- Configure a value using the router-id command.
- Use the highest active interface IP address that is configured on the router.
- Use a loopback interface configured with the highest IP address on the router.
- Use the highest IP address assigned to an active interface participating in the routing process.
218. Which step in the link-state routing process is described by a router running an algorithm to determine the best path to each destination?
- load balancing equal-cost paths
- declaring a neighbor to be inaccessible
- choosing the best route
- executing the SPF algorithm
219. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 192.168.223.0 255.255.254.0. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.1.255
- 0.0.7.255
- 0.0.15.255
- 0.0.31.255
220. What is the format of the router ID on an OSPF-enabled router?
- a unique router host name that is configured on the router
- a unique phrase with no more than 16 characters
- a 32-bit number formatted like an IPv4 address
- an 8-bit number with a decimal value between 0 and 255
- a character string with no space
221. Question as presented:
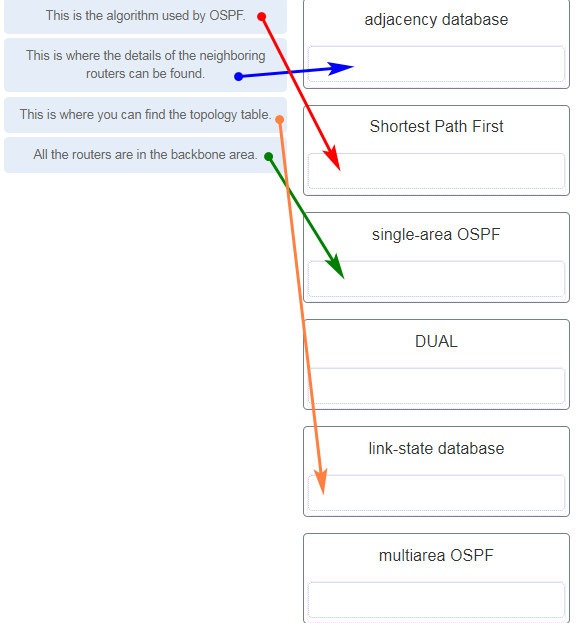
DUAL is the algorithm used by EIGRP. In multiarea OSPF, OSPF is implemented using multiple areas, and all of them must be connected to the backbone area.
222. After modifying the router ID on an OSPF router, what is the preferred method to make the new router ID effective?
- HQ# copy running-config startup-config
- HQ# resume
- HQ# clear ip route *
- HQ# clear ip ospf process
223. In an OSPFv2 configuration, what is the effect of entering the command network 192.168.1.1 0.0.0.0 area 0?
- It allows all 192.168.1.0 networks to be advertised.
- It tells the router which interface to turn on for the OSPF routing process.
- It changes the router ID of the router to 192.168.1.1.
- It enables OSPF on all interfaces on the router.
224. What is the reason for a network engineer to alter the default reference bandwidth parameter when configuring OSPF?
- to force that specific link to be used in the destination route
- to more accurately reflect the cost of links greater than 100 Mb/s
- to enable the link for OSPF routing
- to increase the speed of the link
225. Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which task has to be performed on Router 1 for it to establish an OSPF adjacency with Router 2?
- Issue the clear ip ospf process command.
- Change the subnet mask of interface FastEthernet 0/0 to 255.255.255.0.
- Remove the passive interface command from interface FastEthernet 0/0.
- Add the network 10.0.1.0 0.0.0.255 area 0 command to the OSPF process.
226. Match the description to the term. (Not all options are used.)
227. What is a benefit of multiarea OSPF routing?
- Topology changes in one area do not cause SPF recalculations in other areas.
- Routers in all areas share the same link-state database and have a complete picture of the entire network.
- A backbone area is not required.
- Automatic route summarization occurs by default between areas.
228. Match the OSPF state with the order in which it occurs. (Not all options are used.)
229. What indicates to a link-state router that a neighbor is unreachable?
- if the router no longer receives hello packets
- if the router receives an update with a hop count of 16
- if the router receives an LSP with previously learned information
- if the router no longer receives routing updates
230. Which three OSPF states are involved when two routers are forming an adjacency? (Choose three.)
- Exchange
- Init
- ExStart
- Two-way
- Loading
- Down
231. Refer to the exhibit. Suppose that routers B, C, and D have a default priority, and router A has a priority 0. Which conclusion can be drawn from the DR/BDR election process?
CCNA 3 v7 Modules 1 – 2: OSPF Concepts and Configuration Exam
- If the priority of router C is changed to 255, then it will become the DR.
- Router A will become the DR and router D will become the BDR.
- If the DR fails, the new DR will be router B.
- If a new router with a higher priority is added to this network, it will become the DR.
232. An administrator is configuring single-area OSPF on a router. One of the networks that must be advertised is 64.102.0.0 255.255.255.128. What wildcard mask would the administrator use in the OSPF network statement?
- 0.0.31.255
- 0.0.0.63
- 0.0.63.255
- 0.0.0.127
CCNA 3 Final Exam Answers
1. Which design feature will limit the size of a failure domain in an enterprise network?
- the purchase of enterprise equipment that is designed for large traffic volume
- the installation of redundant power supplies
- the use of a collapsed core design
- the use of the building switch block approach
2. Which two things should a network administrator modify on a router to perform password recovery? (Choose two.)
- the system image file
- the NVRAM file system
- the configuration register value
- the startup configuration file
- system ROM
3. What type of network uses one common infrastructure to carry voice, data, and video signals?
- borderless
- converged
- managed
- switched
4. What are three advantages of using private IP addresses and NAT? (Choose three.)
- hides private LAN addressing from outside devices that are connected to the Internet
- permits LAN expansion without additional public IP addresses
- reduces CPU usage on customer routers
- creates multiple public IP addresses
- improves the performance of the router that is connected to the Internet
- conserves registered public IP addresses
5. Which two scenarios are examples of remote access VPNs? (Choose two.)
- All users at a large branch office can access company resources through a single VPN connection.
- A small branch office with three employees has a Cisco ASA that is used to create a VPN connection to the HQ.
- A toy manufacturer has a permanent VPN connection to one of its parts suppliers.
- A mobile sales agent is connecting to the company network via the Internet connection at a hotel.
- An employee who is working from home uses VPN client software on a laptop in order to connect to the company network.
6. What are three benefits of cloud computing? (Choose three.)
- It utilizes end-user clients to do a substantial amount of data preprocessing and storage.
- It uses open-source software for distributed processing of large datasets.
- It streamlines the IT operations of an organization by subscribing only to needed services.
- It enables access to organizational data anywhere and at any time.
- It turns raw data into meaningful information by discovering patterns and relationships.
- It eliminates or reduces the need for onsite IT equipment, maintenance, and management.
7. What is a characteristic of a single-area OSPF network?
- All routers share a common forwarding database.
- All routers have the same neighbor table.
- All routers are in the backbone area.
- All routers have the same routing table.
8. What is a WAN?
- a network infrastructure that spans a limited physical area such as a city
- a network infrastructure that provides access to other networks over a large geographic area
- a network infrastructure that provides access in a small geographic area
- a network infrastructure designed to provide data storage, retrieval, and replication
9. What is a purpose of establishing a network baseline?
- It creates a point of reference for future network evaluations.
- It provides a statistical average for network performance.
- It checks the security configuration of network devices.
- It manages the performance of network devices.
10. Which type of OSPF packet is used by a router to discover neighbor routers and establish neighbor adjacency?
- link-state update
- hello
- database description
- link-state request
11. Which two statements are characteristics of a virus? (Choose two.)
- A virus has an enabling vulnerability, a propagation mechanism, and a payload.
- A virus can be dormant and then activate at a specific time or date.
- A virus provides the attacker with sensitive data, such as passwords.
- A virus replicates itself by independently exploiting vulnerabilities in networks.
- A virus typically requires end-user activation.
12. Which public WAN access technology utilizes copper telephone lines to provide access to subscribers that are multiplexed into a single T3 link connection?
- ISDN
- DSL
- cable
- dialup
13. A customer needs a metropolitan area WAN connection that provides high-speed, dedicated bandwidth between two sites. Which type of WAN connection would best fulfill this need?
- packet-switched network
- Ethernet WAN
- circuit-switched network
- MPLS
14. A company has contracted with a network security firm to help identify the vulnerabilities of the corporate network. The firm sends a team to perform penetration tests to the company network. Why would the team use debuggers?
- to detect installed tools within files and directories that provide threat actors remote access and control over a computer or network
- to reverse engineer binary files when writing exploits and when analyzing malware
- to obtain specially designed operating systems preloaded with tools optimized for hacking
- to detect any evidence of a hack or malware in a computer or network
15. Consider the following output for an ACL that has been applied to a router via the access-class in command. What can a network administrator determine from the output that is shown?
R1# Standard IP access list 2 10 permit 192.168.10.0, wildcard bits 0.0.0.255 (2 matches) 20 deny any (1 match)
- Two devices connected to the router have IP addresses of 192.168.10. x .
- Two devices were able to use SSH or Telnet to gain access to the router.
- Traffic from one device was not allowed to come into one router port and be routed outbound a different router port.
- Traffic from two devices was allowed to enter one router port and be routed outbound to a different router port.
16. What command would be used as part of configuring NAT or PAT to clear dynamic entries before the timeout has expired?
- clear ip dhcp
- clear ip nat translation
- clear access-list counters
- clear ip pat statistics
17. What are two characteristics of video traffic? (Choose two.)
- Video traffic consumes less network resources than voice traffic consumes.
- Video traffic latency should not exceed 400 ms.
- Video traffic is more resilient to loss than voice traffic is.
- Video traffic requires a minimum of 30 kbs of bandwidth.
- Video traffic is unpredictable and inconsistent.
18. Refer to the exhibit. A technician is configuring R2 for static NAT to allow the client to access the web server. What is a possible reason that the client PC cannot access the web server?
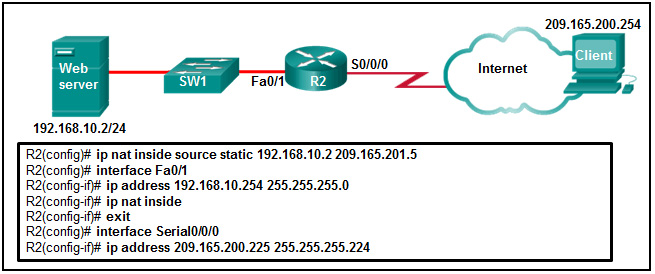
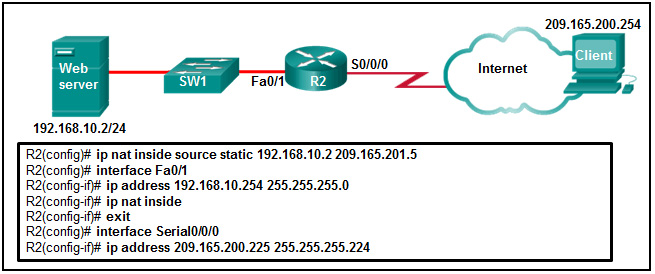
- The IP NAT statement is incorrect.
- Interface Fa0/1 should be identified as the outside NAT interface.
- Interface S0/0/0 should be identified as the outside NAT interface.
- The configuration is missing a valid access control list.
19. In setting up a small office network, the network administrator decides to assign private IP addresses dynamically to workstations and mobile devices. Which feature must be enabled on the company router in order for office devices to access the internet?
- UPnP
- MAC filtering
- NAT
- QoS
20. A data center has recently updated a physical server to host multiple operating systems on a single CPU. The data center can now provide each customer with a separate web server without having to allocate an actual discrete server for each customer. What is the networking trend that is being implemented by the data center in this situation?
- online collaboration
- BYOD
- virtualization
- maintaining communication integrity
21. Refer to the exhibit. Which address or addresses represent the inside global address?
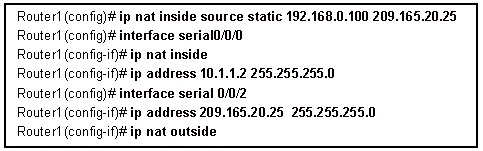
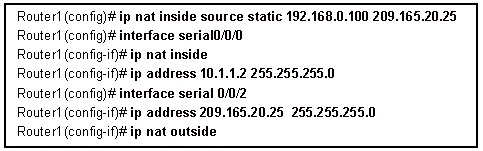
- 192.168.0.100
- 10.1.1.2
- any address in the 10.1.1.0 network
- 209.165.20.25
22. Which two IPsec protocols are used to provide data integrity?
- MD5
- DH
- AES
- SHA
- RSA
23. If an outside host does not have the Cisco AnyConnect client preinstalled, how would the host gain access to the client image?
- The Cisco AnyConnect client is installed by default on most major operating systems.
- The host initiates a clientless VPN connection using a compliant web browser to download the client.
- The host initiates a clientless connection to a TFTP server to download the client.
- The host initiates a clientless connection to an FTP server to download the client.
- leased line
- cable
- digital subscriber line
- Ethernet WAN
- municipal Wi-Fi
- IP precedence
- DSCP
- ToS
- CoS
- Both routers are configured to use NTPv2.
- Router R1 is the master, and R2 is the client
- The IP address of R2 is 192 168.1.2.
- Router R2 is the master, and R1 is the client
- The IP address of R1 is 192.168.1.2
- access-list 105 permit tcp host 10.0.54.5 any eq www
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
28. Refer to the exhibit. If the network administrator created a standard ACL that allows only devices that connect to the R2 G0/0 network access to the devices on the R1 G0/1 interface, how should the ACL be applied?
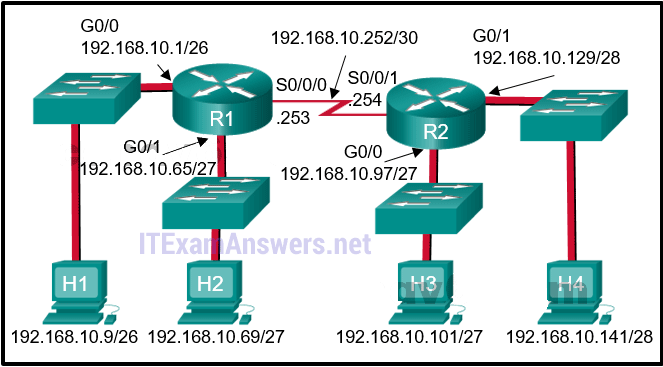
- inbound on the R2 G0/0 interface
- outbound on the R1 G0/1 interface
- inbound on the R1 G0/1 interface
- outbound on the R2 S0/0/1 interface
29. Which is a characteristic of a Type 2 hypervisor?- does not require management console software
- has direct access to server hardware resources
- best suited for enterprise environments
- installs directly on hardware
30. What are the two types of VPN connections? (Choose two.)- PPPoE
- Frame Relay
- site-to-site
- remote access
- leased line
31. Refer to the exhibit. What three conclusions can be drawn from the displayed output? (Choose three.)
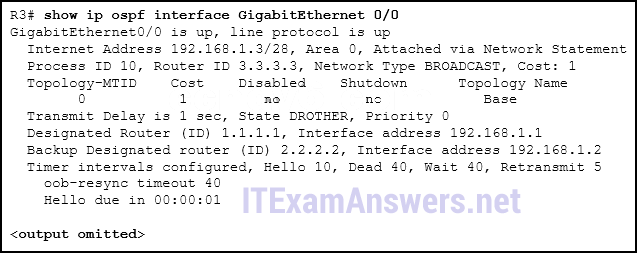
- The DR can be reached through the GigabitEthernet 0/0 interface.
- There have been 9 seconds since the last hello packet sent.
- This interface is using the default priority.
- The router ID values were not the criteria used to select the DR and the BDR.
- The router ID on the DR router is 3.3.3.3
- The BDR has three neighbors.
32. Refer to the exhibit. A network administrator is configuring an ACL to limit the connection to R1 vty lines to only the IT group workstations in the network 192.168.22.0/28. The administrator verifies the successful Telnet connections from a workstation with IP 192.168.22.5 to R1 before the ACL is applied. However, after the ACL is applied to the interface Fa0/0, Telnet connections are denied. What is the cause of the connection failure?
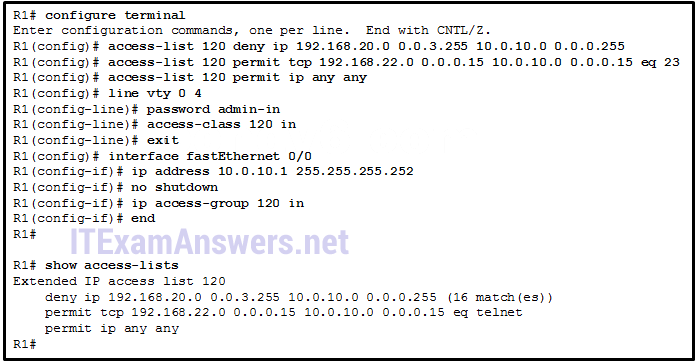
- The enable secret password is not configured on R1.
- The IT group network is included in the deny statement.
- The permit ACE specifies a wrong port number.
- The permit ACE should specify protocol ip instead of tcp.
- The login command has not been entered for vty lines.
33. What functionality does mGRE provide to the DMVPN technology?- It allows the creation of dynamically allocated tunnels through a permanent tunnel source at the hub and dynamically allocated tunnel destinations at the spokes.
- It provides secure transport of private information over public networks, such as the Internet.
- It is a Cisco software solution for building multiple VPNs in an easy, dynamic, and scalable manner.
- It creates a distributed mapping database of public IP addresses for all VPN tunnel spokes.
34. What is used to pre-populate the adjacency table on Cisco devices that use CEF to process packets?- the FIB
- the routing table
- the ARP table
- the DSP
35. What command would be used as part of configuring NAT or PAT to display information about NAT configuration parameters and the number of addresses in the pool?- show running-config
- show ip nat statistics
- show ip cache
- show version
36. What is a purpose of establishing a network baseline?- It provides a statistical average for network performance.
- It creates a point of reference for future network evaluations.
- It manages the performance of network devices.
- It checks the security configuration of network devices.
37. Match the type of WAN device or service to the description. (Not all options are used.)CPE —> devices and inside wiring that are located on the enterprise edge and connect to a carrier link
DCE —> devices that provide an interface for customers to connect to within the WAN cloud
DTE —> customer devices that pass the data from a customer network for transmission over the WAN
local loop —> a physical connection from the customer to the service provider POP
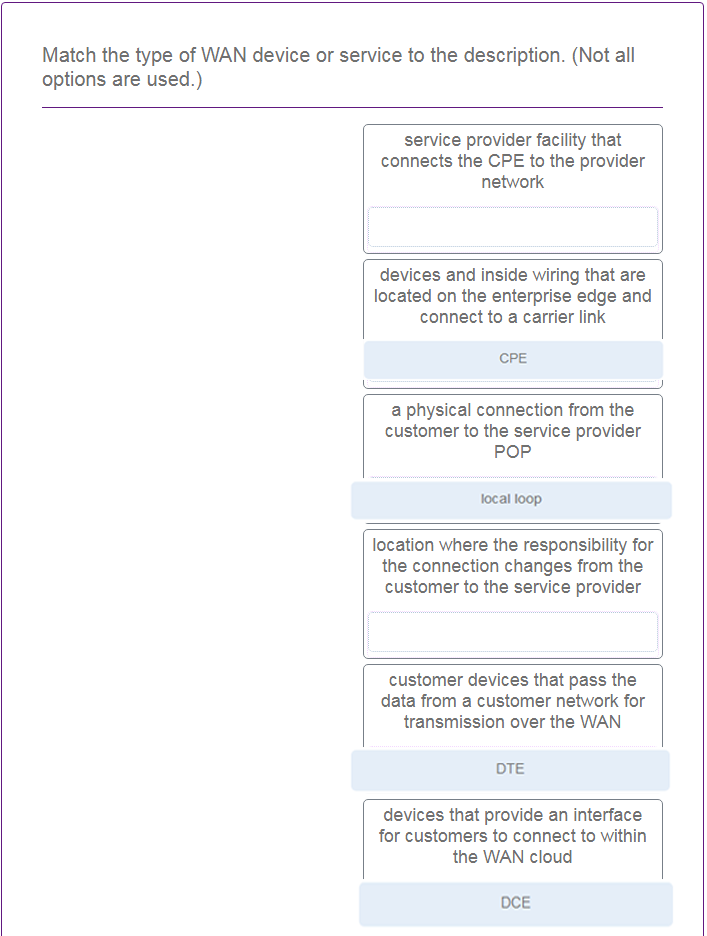 38. Which statement describes a characteristic of standard IPv4 ACLs?
38. Which statement describes a characteristic of standard IPv4 ACLs?- They filter traffic based on source IP addresses only.
- They can be created with a number but not with a name.
- They are configured in the interface configuration mode.
- They can be configured to filter traffic based on both source IP addresses and source ports.
39. Refer to the exhibit. R1 is configured for NAT as displayed. What is wrong with the configuration?
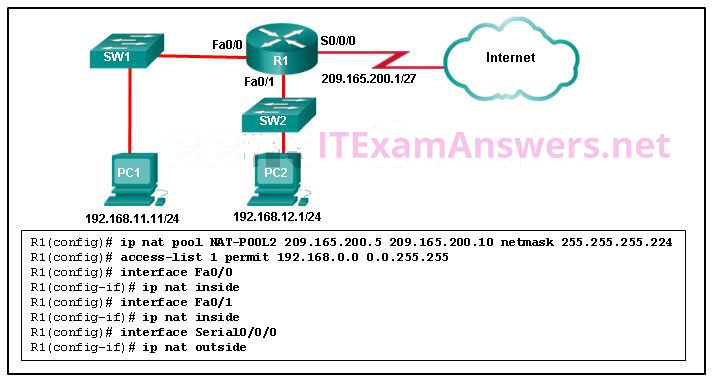
- NAT-POOL2 is not bound to ACL 1.
- Interface Fa0/0 should be identified as an outside NAT interface.
- The NAT pool is incorrect.
- Access-list 1 is misconfigured.
40. Refer to the exhibit. What method can be used to enable an OSPF router to advertise a default route to neighboring OSPF routers?
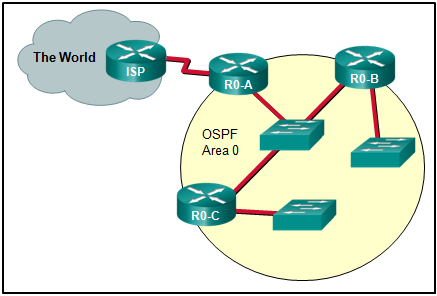
- Use a static route pointing to the ISP and redistribute it.
- Use a static route pointing to the ISP and redistribute it.
- Use the redistribute static command on R0-A.
- Use the default-information originate command on ISP.
- Use the default-information originate command on R0-A.
24. A company is considering updating the campus WAN connection. Which two WAN options are examples of the private WAN architecture? (Choose two.)
25. Which type of QoS marking is applied to Ethernet frames?
26. Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2? (Choose two.)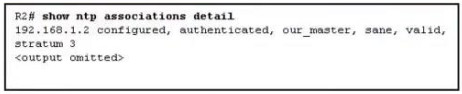
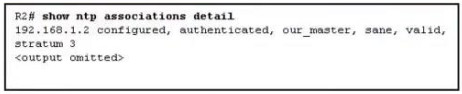
27. Refer to the exhibit. The network administrator that has the IP address of 10.0.70.23/25 needs to have access to the corporate FTP server (10.0.54.5/28). The FTP server is also a web server that is accessible to all internal employees on networks within the 10.x.x.x address. No other traffic should be allowed to this server. Which extended ACL would be used to filter this traffic, and how would this ACL be applied? (Choose two.)
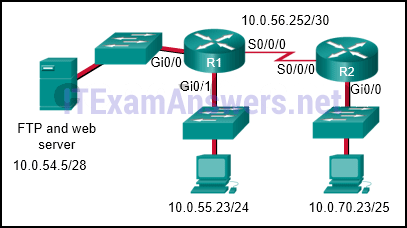
R1(config)# interface s0/0/0
R1(config-if)# ip access-group 105 outR2(config)# interface gi0/0
R2(config-if)# ip access-group 105 in
R1(config-if)# ip access-group 105 outR2(config)# interface gi0/0
R2(config-if)# ip access-group 105 in
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
access-list 105 permit tcp 10.0.0.0 0.255.255.255 host 10.0.54.5 eq www
access-list 105 deny ip any host 10.0.54.5
access-list 105 permit ip any any
access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21
access-list 105 permit tcp 10.0.0.0 0.255.255.255 host 10.0.54.5 eq www
access-list 105 deny ip any host 10.0.54.5
access-list 105 permit ip any any
access-list 105 permit ip host 10.0.70.23 host 10.0.54.5
access-list 105 permit tcp any host 10.0.54.5 eq www
access-list 105 permit ip any any
access-list 105 permit tcp any host 10.0.54.5 eq www
access-list 105 permit ip any any
R1(config)# interface gi0/0
R1(config-if)# ip access-group 105 out*
R1(config-if)# ip access-group 105 out*