reduced network downtime
faster time to resolution of problems
simplified troubleshooting processes
predictable lead times for change requests
maintenance windows during regular business hours
2. RSPAN depends on which type of VLAN?
native VLAN
management VLAN
default VLAN
RSPAN VLAN
black hole VLAN
private VLAN
3.
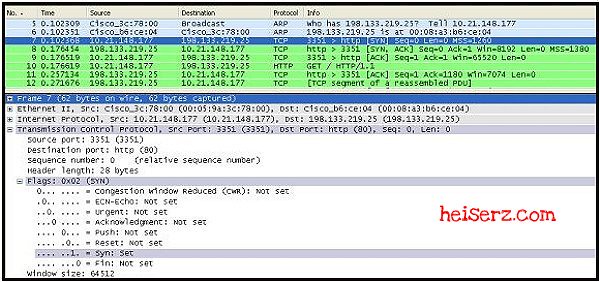
Refer to the exhibit. What information can be deduced from the provided debug aaa accounting command output?
The user successfully gained access to the router EXEC shell.
The user attempts to gain access to a local security server were unsuccessful.
The user credentials were rejected by the default authentication method.
The user access to the services was stopped because of the improper protocol that was used for the session.
4.
Refer to the exhibit. A network administrator issues the show interfaces s0/0/0 command on a router to determine the cause for a recent decrease in device performance. Based on the output shown, what is a possible cause of the observed performance issues?
high CPU usage on the router
insufficient RAM in the router
incorrect or outdated version of the Cisco IOS
unrecognized Layer 2 encapsulation formats on the network
5. In which three situations will traffic be handed off (punted) to the CPU for processing? (Choose three.)
any traffic that is going through a GRE tunnel
any traffic that is explicitly blocked by an ACL
any traffic that is destined for any of the switch IP addresses
any traffic that is assigned to a particular VLAN that is not allowed on a trunk
any traffic that is coming to an inbound port that is in the spanning-tree blocking state
any multicast and broadcast traffic that is coming from the Spanning Tree Protocol (STP) or routing protocols
6. An administrator has just implemented two-way route redistribution between an OSPF and EIGRP domain. However, network performance between domains quickly degraded and an investigation revealed routing loops. What action could be used to solve this issue?
Change the seed metric of the routes being redistributed.
Filter the routes being redistributed between the protocols.
Redistribute all subnets in both EIGRP and OSPF domains.
Configure an additional router to be a secondary point of route redistribution.
7. What content can be found in the show ip eigrp topology network mask output?
minimum delay
cumulative cost
hop count
variance
metric weights
8.
Refer to the exhibit. BPDU guard and PortFast have been configured on all edge ports on the access switches. A junior network administrator tested a new switch in the lab and verified that the bridge ID is 32887. What would happen when the administrator plugs this switch into port Fa0/20 on ASW_1 in an attempt to extend the LAN?
Port Fa0/20 will be shut down.
Port Fa0/20 will become a root port.
Port Fa0/20 will start forwarding traffic immediately.
Port Fa0/20 will transition from blocking to forwarding state after the spanning tree convergence.
9. What is a characteristic of network maintenance?
Network maintenance typically excludes consideration of network changes.
Proper network maintenance will eliminate network downtime.
Maintaining network documentation is an important element of network maintenance.
The amount of resources expended on network maintenance is consistent across all companies.
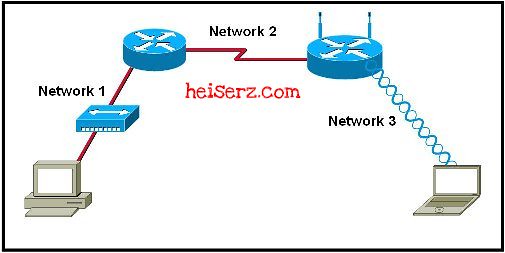
10.
Refer to the exhibit. A network administrator is troubleshooting a connectivity issue between LAN clients on routers R1 and R3. Connectivity tests from R2 to the R1 and R3 LAN segments are successful. The administrator issues the debug ip icmp command for R1 and confirms that a routing issue exists. Based on the information that is presented in the exhibit, which configuration command would correct the problem?
R1(config)# ip route 0.0.0.0 0.0.0.0 172.16.7.1
R1(config)# ip route 172.16.6.0 255.255.255.0 172.16.7.10
R2(config)# ip route 172.16.6.0 255.255.255.0 172.16.7.9
R2(config)# ip route 0.0.0.0 0.0.0.0 172.16.7.9
R3(config)# ip route 0.0.0.0 0.0.0.0 172.16.7.9
R3(config)# ip route 172.16.6.0 255.255.255.0 172.16.7.10
11. What is the final task in a structured troubleshooting process?
gathering information
testing the hypothesis
documenting the changes
eliminating possible causes
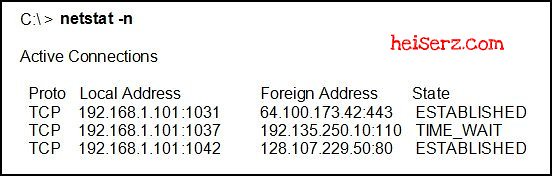
12. Syslogs reveal malicious activity originating from an internal host that is located at IP address 10.10.10.251. From the local gateway router, the administrator successfully pings the host IP address and populates the ARP cache of the router. The administrator then issues the show ip arp 10.10.10.251 command and discovers that the MAC address of the host is 0011.9254.e2a0. What could the administrator do next to discover the physical location of the malicious host?
Issue the show mac address-table address 0011.9254.e2a0 command on various switches and follow the path to the host.
Issue the show vlan command on various switches and follow the path to the host.
Issue the traceroute 0011.9254.e2a0 command and follow the path to the host.
Issue the traceroute 10.10.10.251 command and follow the path to the host.
13. Which two pieces of information are displayed by the debug ip bgp command? (Choose two.)
BGP updates
route redistribution information
BGP related events
phases of BGP peering relationships
internal metrics of IBGP routes
14.
Refer to the exhibit. What could be concluded about the TACACS+ failure based on the exhibited command output from debug tacacsand debug aaa authentication?
The TACACS+ server is not operational.
The TACACS+ server IP address has been incorrectly configured on the router.
The TACACS+ server key of the router does not match that of the TACACS+ server.
The username and password that were supplied by the user were rejected by the TACACS+ server.
15
Refer to the exhibit. A network administrator issued the debug dhcp detail command to verify the operations of DHCP on router R2. Which statement is correct about the active DHCP processes on R2?
The DHCP server sends a DHCPOFFER message with the full set of configuration parameters to the client.
The DHCP client sends out a DHCPDISCOVER broadcast message to find its local DHCP server.
The DHCP server sends a DHCPACK message with the full set of configuration parameters to the client.
The DHCP client sends out a DHCPREQUEST broadcast message to the DHCP server to accept the offered parameters.
16. Which two benefits do the use of templates provide in the troubleshooting process? (Choose two.)
provide an effective method of maintaining network documentation
ensure that all individuals carry out similar tasks in a consistent manner
document the solution to specific problems eliminating the requirement for troubleshooting
allow each technician to select the best troubleshooting process to use for a particular problem
ensure that the problem is located and corrected regardless of the knowledge level of the technician
17. Which VTP mode is configured on a switch in the implementation of private VLANs?
client
server
transparent
client or server
client or transparent
transparent or server
18. A network administrator notices frames are received on a different port than expected on a switch. What are two plausible causes of the problem? (Choose two.)
a routing error
an access list error
duplicate MAC addresses
VLAN trunk misconfiguration
a Spanning Tree Protocol related issue
19. What are the three private VLAN (PVLAN) port types? (Choose three.)
community
edge
isolated
point-to-point
promiscuous
protected
20.
Refer to the exhibit. Based on the information that is provided, which two NetFlow statements are correct? (Choose two.)
All NetFlow packets sent from R1 to the traffic collector will be sourced from IP address 1.1.1.1.
Interfaces Fa0/0 and Fa0/1 must also be included as flow-export source interfaces.
NetFlow version 5 should be configured if the infrastructure includes non-Cisco devices.
NetFlow will track all ingress traffic for interfaces Fa0/0 and Fa0/1.
NetFlow will forward the traffic statistics and packet payload content of interfaces Fa0/0 and Fa0/1 to IP address 10.10.10.1.
The UDP value 9996 is optional because it is the default NetFlow destination port number.
21.
Refer to the exhibit. A network administrator is troubleshooting a NAT translation issue on router R2. The IP addresses of hosts on the R2 LAN are not being translated by R2. Based on the information in the exhibit, what is the issue?
The NAT pool is exhausted.
The static translation prevents any new dynamic translations.
The ACL is using a wrong pool reference.
The R2 LAN is not configured as an inside interface.
22.
Refer to the exhibit. An administrator has configured VRRP on routers R1 and R2. However, no output is generated using the show vrrp brief command on router R1. The administrator then verifies the VRRP interface and key chain configurations. Based on the output in the exhibit, what is the cause of the problem?
Interface FastEthernet 0/0 on router R1 requires the vrrp 1 ip 10.1.1.254 command to be issued.
Interface FastEthernet 0/0 on router R1 requires the vrrp 1 preempt command to be issued.
Interface FastEthernet 0/0 on router R1 requires the vrrp 1 priority 100 command to be issued.
Router R1 is configured to use text authentication, while R2 is configured to use MD5 authentication.
Router R1 should be configured to use text authentication.
23.
Refer to the exhibit. A network administrator is investigating a possible network congestion problem. Which information is indicative of network congestion?
The EIGRP neighbor has not sent any hello packets in the last 14 seconds.
The EIGRP neighbor is redistributing routes from OSPF with invalid seed metrics.
The EIGRP neighbor is offline and unreachable.
The Q Cnt field should be at zero.
The Seq Num field should be much higher.
The values of the SRTT and RTO fields should be much lower.
24. Which DHCP message is sent by the server to the client and contains the DHCP configuration parameters?
DHCP DISCOVER
DHCP OFFER
DHCP REQUEST
DHCP ACK
DHCP NAK
DHCP INFORM
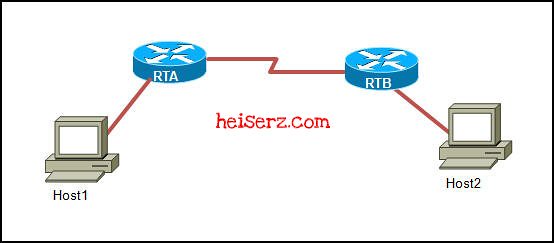
25. Which statement is true based on the show ip ospf neighbor command output that is shown in the exhibit?
RTB did not see its router ID in the hello packet that was received from RTA.
RTB did not receive a hello packet from RTA.
RTB is able to exchange routing updates with RTA.
RTB has established an adjacency with RTA.
26.
Refer to the exhibit. A network administrator is troubleshooting a connectivity issue between R1 and R2. The routers are failing to create a neighbor relationship and no OSPF HELLO packets are traversing the Frame Relay link. Based on the output, what does the administrator need to do on R1 to correct the issue?
Map the DLCI to the link local address of R2.
Change the OSPF neighbor to point to the global unicast address of R2.
Change the IPv6 address on Serial 0/0/0 to be in the same segment as the Serial 0/0/0 interface of R2.
Remove the broadcast keyword from the frame-relay map statement.
27.
Refer to the exhibit. You have been asked to troubleshoot a connectivity issue between R3 and R1. From the partial output of theshow running-config command on both routers, what configuration change is required?
A static route should be added to R3 to point to the 192.168.1.0/24 network.
A static route should be added to R1 to point to the 192.168.1.0/24 network.
The tunnel source for Tunnel0 on R3 should be the IP address of Serial0/0/1 on R1.
The tunnel source for Tunnel0 on R1 should be the IP address of Loopback0 on R3.
The tunnel destination for Tunnel0 on R1 should be the IP address of Serial0/0/1 on R3.
The tunnel destination for Tunnel0 on R3 should be the IP address of Loopback0 on R1.
28. Which type of spanning tree failure is the most disruptive?
The STP reaches its maximum diameter.
Ports that should be blocked start forwarding.
The TTL field in the Ethernet frames decrements to 0 on all frames.
Frames with matching entries in the MAC address table are not forwarded.
29.
Refer to the exhibit. Wireless network users are complaining about performance issues, especially when using Voice over WLAN. Based on the output that is shown, what could be the problem?
QoS is not supported in Lightweight mode.
The trunk between R1 and SW1 does not support QoS.
SW1 is resetting the DSCP values supplied by the Lightweight AP.
The Wireless LAN Controller has not been configured to support voice traffic.
QoS has not been enabled between the Lightweight AP and the Wireless LAN Controller.
30. Which backup mechanism presents the highest security risk?
FTP
HTTPS
SCP
TFTP
31. An administrator notices that CDP is disabled on a port that connects to an IP phone. What effect will this have?
The phone will experience intermittent connectivity.
The phone will be placed into the default VLAN.
The phone will not be able to discover auxiliary VLAN information, QoS settings, or automatically negotiate power settings.
The phone will be able to make calls but will not be able to receive calls.
32. Which two conditions could cause two routers to have trouble establishing a neighbor relationship in an OSPF network? (Choose two.)
The interfaces have different network types.
Hello packets are not sent from either neighbor.
One of the routers is redistributing the OSPF routes into EIGRP.
Slow network connections cause OSPF advertisements to time out.
The network command has put the connected interfaces into the same OSPF area.
33.
Refer to the exhibit. A port channel link between a branch site and the main site experiences an outage after a hardware upgrade at the branch site. The network administrator at the main site checks the log and sees a “%SPANTREE-2-CHNL_MISCFG” message. What is a likely cause of this message?
The branch site has been configured for the Spanning Tree Protocol, but the main site has not.
The main site has been configured to bundle links into an EtherChannel and the branch site has not.
The branch site is running a newer, incompatible version of the Spanning Tree Protocol.
The main site has inconsistencies in the physical ports that are members of the channel.
34.
Refer to the exhibit. Based on the output of the debug ip nat command in the exhibit, which two statements are true? (Choose two.)
Packets were not translated for the return path from source 192.168.1.95.
Packets that are destined for 172.31.2.132 from source 192.168.1.95 are translated into 172.31.233.209.
Entries that are indicated with NAT* have been translated via the fast path.
The IP address 172.31.233.209 is the configured IP address on the remote PC.
Entries with NAT* have the ToS value 5.
35. When configuring private VLANs, how many isolated VLANs can be mapped to a primary VLAN?
0
1
2
4
platform dependent
36. Which switch error is indicative of a duplex mismatch on the full-duplex side of a link?
Xmit-Err
Rcv-Err
FCS-Err
Giants
37. Refer to the exhibit. Users are complaining that they are unable to access the web server that is located at 172.16.1.101. Based on the partial syslog output that is exhibited, what is causing this problem?
The web server is denying the client request.
There is no logical path from the client to the web server location.
A Java applet reset option is configured on the zone-based policy firewall.
The zone-based policy firewall has been configured to block all HTTP traffic to the server location.
The classic IOS firewall has not been properly configured to allow HTTP traffic in response to an internal request.
38. Which action occurs immediately following POST in the boot process of a Cisco IP phone?
The IP phone sends DHCP broadcasts.
The IP phone initializes the IP stack.
The IP phone uses CDP to learn the voice VLAN.
The IP phone requests a configuration file from a TFTP server.
39. What occurs when the no service password-recovery command is entered on the router?
Passwords will not be encrypted.
Executive passwords can be retrieved and viewed in the running configuration.
Executive passwords can be changed in ROMMON mode.
The original configuration and passwords cannot be retrieved.
All passwords are encrypted to level 7.
40. Which anti-spoofing mechanism will filter packets that enter a multilayer switch through an interface that does not provide the best path back to the source of the packet?
spanning tree
private VLAN
intrusion prevention
VLAN access control lists
Unicast Reverse Path Forwarding
41. Which DSCP value should be applied to voice traffic?
AF11
AF31
CS1
EF
42. Which command would a network administrator use to verify which VLANs are allowed on a trunk?
show vlan
show interfaces trunk
show vlan interface
show mac address-table
43.
Refer to the exhibit. An administrator is troubleshooting an HSRP implementation on routers R1 and R2. Based on the output in the exhibit, what is the probable cause of the problem?
Router R1 requires the standby 1 ip 10.1.1.254 command to be issued on interface FastEthernet 0/0.
Router R2 requires the standby 1 ip 10.1.1.254 command to be issued on interface FastEthernet 0/0.
Router R1 is configured to support MD5 authentication while router R2 is configured to support text authentication.
Router R1 is configured to support text authentication while router R2 is configured to support MD5 authentication.
Routers R1 and R2 have different MD5 authentication strings configured.
Routers R1 and R2 have different text authentication strings configured.
44. What are two problems that can occur when routes are redistributed in two directions? (Choose two.)
suboptimal routing
routing loops
lost seed metrics
route filtering
lost external routes
45.
Refer to the exhibit. Which two FTP-related statements are true? (Choose two.)
The Configuration Rollback feature was preconfigured on router R1 via the archive command.
The configuration was copied using a method that is less secure than HTTPS.
The ip ftp username and ip ftp password commands were issued on router R1.
The login credentials were sent to the FTP server in an encrypted format.
The R1-test.cfg configuration was successfully copied from the FTP server to the running configuration file of router R1.
The R1-test.cfg configuration was successfully copied from the FTP server to the startup configuration file of router R1.
46.
Refer to the exhibit. Users are complaining that they are unable to connect to resources outside of their corporate network during peak hours. What action should the administrator take to correct this problem?
Remove the ACL because it is blocking connections.
Change the FastEthernet 0/1 interface to an inside NAT interface.
Disable CEF because it is sending packets to the CPU for processing.
Disable static NAT because it is interfering with the dynamic translations.
Increase the size of the NAT pool to provide more IP addresses for translation.
47.
Refer to the exhibit. A network administrator is trying to secure the remote administration of the router by enabling the use of the SSH protocol. Which changes should be made on the partial configuration as shown in the graphic?
The enable password must be encrypted.
The commands listed under the VTY line should be listed under the Console line.
The transport input telnet command should be changed to transport input ssh.
The transport input telnet command should be changed to transport input none.
48. Users at a branch office are complaining that they are unable to connect to resources at the head office. The network administrator issues the show ip route command and verifies that the correct next hop IP address and egress interface are listed. What should the administrator do next?
Verify that CEF is running on the router.
Verify the Layer 3 to Layer 2 mappings.
Verify end-to-end connectivity via the use of the ping command.
Verify that the information in the CEF FIB is correct.
Verify that the interface is active and participating in the routing process.
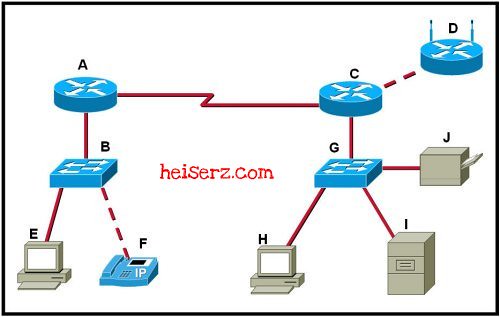
49.
Refer to the exhibit. In a converged spanning tree, how many blocked ports will there be in VLAN 1 for the pictured topology?
1
2
3
4
50.
Refer to the exhibit. Users are complaining that they are receiving duplicate address error messages when they start their machines. What should the administrator do to correct this problem?
Change the address assigned to the default router and dns server.
Decrease the DHCP lease time to make more addresses available at one time.
Change the netmask to 255.0.0.0 to agree with the class A network that is used in the DHCP pool.
Use the ip dhcp excluded-address command to exclude any statically assigned addresses from the DHCP pool.
51. What is a characteristic of network maintenance toolkits?
are vendor specific
may be both GUI and CLI
require expensive investments
support only real-time monitoring
52. What can be inferred from the fact that a switch is receiving BPDUs on a port but not transmitting BPDUs?
The port is a designated port.
The port is a root port.
The port is disabled.
The port is in listening state.
53. A newly configured switch is connected to an existing network. The instant the trunk link is brought up to the rest of the network, the entire network goes down. What could have caused this problem?
The switch was inserted into the network using an incorrect VTP domain name.
The VTP password entered on the new switch did not match that of the existing VTP domain.
The switch should have been placed into VTP Transparent Mode prior to being inserted into the network.
The configuration revision number of the inserted switch was higher than the configuration revision of the VTP domain.
The configuration revision number of the inserted switch was lower than the configuration revision of the VTP domain.
54.
Refer to the exhibit. A network engineer is investigating a reported issue of Computer1 not receiving its IP configuration from the DHCP server. Computer2 is receiving its configuration from the DHCP server. What is a plausible reason for this issue?
An ACL is blocking broadcasts into the F0/0 interface of router North .
The DHCP server does not have a DHCP pool for 192.168.0.0 /24 network.
The WAN segment between routers East and North should be replaced with a LAN.
The S0/0/0 interface of router East should be configured to provide DHCP relay.
55.
Refer to the exhibit. Based on the output that is generated, which two statements are true? (Choose two.)
The archive path is the only mandatory archive parameter that must be configured.
Every time the running configuration file is saved to NVRAM, it will also be automatically archived.
The $h and $t parameters will automatically add the device hostname and version number to the archive filename.
Use the archive config privileged EXEC mode command to replace the running configuration file with the most recent archived file.
The time-period parameter must be configured to enable the automatic archiving of the running-configuration file everytime it is saved to NVRAM.
56. What are two limitations of using buffered logging? (Choose two.)
Only high severity messages can be captured.
Messages are lost when there is a connectivity issue.
Log messages are removed when a device is powered down.
Message services may have messages filtered through a firewall.
Oldest messages are overwritten when allocated memory is exceeded.
57.
Refer to the exhibit. You have been asked to correct the configuration on R1 so that the Tunnel 0 interface does not flap and R3 can be consistently reached from R1. What command would you issue on R1 to accomplish this?
ip route 10.3.3.3 255.255.255.255 Tunnel0
ip route 10.3.3.3 255.255.255.255 Serial0/0/0
ip route 172.16.25.3 255.255.255.0 Serial0/0/0
ip route 172.16.25.0 255.255.255.0 Serial0/0/0
ip route 172.16.25.3 255.255.255.255 Tunnel0
ip route 172.16.15.2 255.255.255.255 Tunnel0
58. What type of BGP message precedes the successful formation of a BGP peering session?
update
keepalive
established
withdraw
open
59.
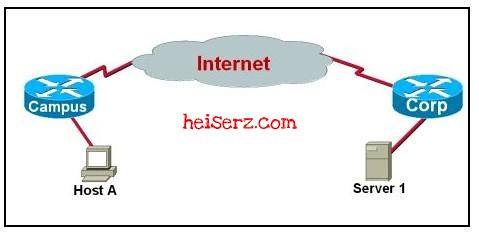
Refer to the exhibit. A network administrator is unable to have two BGP peers exchange routing information. Which solution would correct this problem?
Change the neighbor peer IP addresses on R1 and R2 to the loopback interface IP address of the other router.
Change the neighborx.x.x.xupdate-source command on R1 and R2 to refer to the FastEthernet interfaces.
Enter the neighborx.x.x.xebgp-multihop 1 command on R1 and R2.
Remove the loopback interfaces on each router.
60.
Refer to the exhibit. Based on the partial configuration that is shown, which traffic will be inspected by the zone-based policy firewall?
all TCP traffic that is destined for the public network
all TCP traffic that is destined for the private network
Telnet, SMTP, and HTTP traffic that is destined for the public network
Telnet, SMTP, and HTTP traffic that is destined for the private network