1. A client sends a request for an IP address to a DHCP server. Which DHCP message to the client will provide the configuration parameters that include an IP address, a domain name, and a lease for the IP address?
DHCPDISCOVER
DHCPOFFER
DHCPREQUEST
DHCPACK
DHCPOFFER
DHCPREQUEST
DHCPACK
2. A DHCPREQUEST message has been sent from the client to the DHCP server. What information is included in the message?
initial message to locate a DHCP server
formal request for the offered IP address
confirmation that the IP address has been allocated to the client
denial message to reject the first offer from the DHCP server
initial message to locate a DHCP server
formal request for the offered IP address
confirmation that the IP address has been allocated to the client
denial message to reject the first offer from the DHCP server
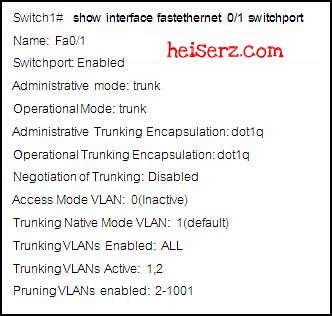
3.
Refer to the exhibit. The router has been properly configured for the trunking interface. Which statement is true about the routing table on the router?
It will show a next hop address of the switch for both VLANs.
It will show one trunking route to 10.0.0.0/8.
It should contain routes to the 10.10.10.0/24 and the 10.10.11.0/24 networks.
Because the switch is not configured properly to trunk VLAN 1 and VLAN 2, the routing table of the router will not show routes to either VLAN .
Because the switch port fa0/1 is in access mode, the routing table of the router will not show any routes.
Refer to the exhibit. The router has been properly configured for the trunking interface. Which statement is true about the routing table on the router?
It will show a next hop address of the switch for both VLANs.
It will show one trunking route to 10.0.0.0/8.
It should contain routes to the 10.10.10.0/24 and the 10.10.11.0/24 networks.
Because the switch is not configured properly to trunk VLAN 1 and VLAN 2, the routing table of the router will not show routes to either VLAN .
Because the switch port fa0/1 is in access mode, the routing table of the router will not show any routes.
4. What is an advantage to using a trunk link to connect a switch to an external router that is providing inter-VLAN routing?
works with any switch that supports VLANs and trunking
lowers latency
provides redundancy to the VLANs
reduces CPU overhead
works with any switch that supports VLANs and trunking
lowers latency
provides redundancy to the VLANs
reduces CPU overhead
5.
Refer to the exhibit and the partial configuration taken on router RTA. Users on VLAN 5 cannot communicate with theusers on VLAN 10. What should be done to fix the problem?
A dynamic routing protocol should be configured on the router.
Two static routes should be configured on the router, each pointing to each subnet.
The Fa0/0 interface should be configured with a primary IP address of 10.10.5.1/24 and a secondary IP address of 10.10.10.1/24.
The subinterfaces of the router should be configured with 802.1Q encapsulation.
Refer to the exhibit and the partial configuration taken on router RTA. Users on VLAN 5 cannot communicate with theusers on VLAN 10. What should be done to fix the problem?
A dynamic routing protocol should be configured on the router.
Two static routes should be configured on the router, each pointing to each subnet.
The Fa0/0 interface should be configured with a primary IP address of 10.10.5.1/24 and a secondary IP address of 10.10.10.1/24.
The subinterfaces of the router should be configured with 802.1Q encapsulation.
6.
Refer to the exhibit. Based on the debug ip dhcp server packet output, which statement is true?
The client sends a DHCPDISCOVER that contains IP address 10.1.10.21 to the DHCP server.
The client sends a DHCPREQUEST that contains IP address 10.1.10.21 to the DHCP server.
The client sends the BOOTREPLY broadcast message to inquire for a new IP address.
The client accepts the offer from the DHCP server for the 10.1.10.21 IP address.
Refer to the exhibit. Based on the debug ip dhcp server packet output, which statement is true?
The client sends a DHCPDISCOVER that contains IP address 10.1.10.21 to the DHCP server.
The client sends a DHCPREQUEST that contains IP address 10.1.10.21 to the DHCP server.
The client sends the BOOTREPLY broadcast message to inquire for a new IP address.
The client accepts the offer from the DHCP server for the 10.1.10.21 IP address.
7.
Refer to the exhibit. Which statement is true regarding the diagram and show ip route command output?
Because no routing protocol has been configured, the router will not forward packets between workstations.
The default gateway for hosts on VLAN 10 should be the Fa0/0 IP address of the router.
The default gateway for hosts on VLAN 10 should be the Fa0/0.1 IP address of the router.
The default gateway for hosts on VLAN 10 should be the Fa0/0.2 IP address of the router.
Because their packets are being trunked, hosts on VLAN 10 do not need a default gateway.
Refer to the exhibit. Which statement is true regarding the diagram and show ip route command output?
Because no routing protocol has been configured, the router will not forward packets between workstations.
The default gateway for hosts on VLAN 10 should be the Fa0/0 IP address of the router.
The default gateway for hosts on VLAN 10 should be the Fa0/0.1 IP address of the router.
The default gateway for hosts on VLAN 10 should be the Fa0/0.2 IP address of the router.
Because their packets are being trunked, hosts on VLAN 10 do not need a default gateway.
8. Which two statements are true about routed ports on a multilayer switch? (Choose two.)
A routed port behaves like a regular router interface and supports VLAN subinterfaces.
A routed port is a physical switch port with Layer 2 capability.
A routed port is not associated with a particular VLAN.
To create a routed port requires removal of Layer 2 port functionality with the no switchport interface configurationcommand.
The interface vlan global configuration command is used to create a routed port.
A routed port behaves like a regular router interface and supports VLAN subinterfaces.
A routed port is a physical switch port with Layer 2 capability.
A routed port is not associated with a particular VLAN.
To create a routed port requires removal of Layer 2 port functionality with the no switchport interface configurationcommand.
The interface vlan global configuration command is used to create a routed port.
9. Which two statements are true about switched virtual interfaces (SVI) on a multilayer switch? (Choose two.)
An SVI behaves like a regular router interface but does not support VLAN subinterfaces.
An SVI is a physical switch port with Layer 3 capability.
By default, an SVI is created for the default VLAN (VLAN1).
Only one SVI can be associated with a VLAN.
To create an SVI requires removal of Layer 2 port functionality with the no switchport interface configuration command.
An SVI behaves like a regular router interface but does not support VLAN subinterfaces.
An SVI is a physical switch port with Layer 3 capability.
By default, an SVI is created for the default VLAN (VLAN1).
Only one SVI can be associated with a VLAN.
To create an SVI requires removal of Layer 2 port functionality with the no switchport interface configuration command.
10. Which three statements about a routed switch interface are true? (Choose three.)
A routed switch port is a physical device that is associated with several VLANs.
A routed switch port is created by configuring a Layer 2 port with the no switchport interface configuration commandand assigning an IP address.
A routed switch port is created by entering VLAN interface configuration mode and assigning an IP address.
A routed switch port is a virtual Layer 3 interface that can be configured for any VLAN that exists on a Layer 3 switch.
A routed switch port provides an interface that may provide a Layer 3 connection to a next-hop router.
A routed switch port can serve as a default gateway for devices.
A routed switch port is a physical device that is associated with several VLANs.
A routed switch port is created by configuring a Layer 2 port with the no switchport interface configuration commandand assigning an IP address.
A routed switch port is created by entering VLAN interface configuration mode and assigning an IP address.
A routed switch port is a virtual Layer 3 interface that can be configured for any VLAN that exists on a Layer 3 switch.
A routed switch port provides an interface that may provide a Layer 3 connection to a next-hop router.
A routed switch port can serve as a default gateway for devices.
11.
Refer to the exhibit and the partial configuration taken on routers RTA and RTB. All users can ping their gateways, but users on VLAN 5 and VLAN 10 cannot communicate with the users on VLAN 20. What should be done to solve the problem?
A dynamic routing protocol or static routes should be configured on the routers.
A trunk should be configured between routers RTA and RTB.
RTA interface Fa0/1 and RTB Fa0/1 should be configured with three subinterfaces, each with ISL encapsulation.
RTA interface Fa0/1 and RTB Fa0/1 should be configured with three subinterfaces, each with 802.1Q encapsulation.
Refer to the exhibit and the partial configuration taken on routers RTA and RTB. All users can ping their gateways, but users on VLAN 5 and VLAN 10 cannot communicate with the users on VLAN 20. What should be done to solve the problem?
A dynamic routing protocol or static routes should be configured on the routers.
A trunk should be configured between routers RTA and RTB.
RTA interface Fa0/1 and RTB Fa0/1 should be configured with three subinterfaces, each with ISL encapsulation.
RTA interface Fa0/1 and RTB Fa0/1 should be configured with three subinterfaces, each with 802.1Q encapsulation.
12. Which statement describes what occurs when a DHCP request is forwarded through a router that has been configured with the ip helper-address command?
The router replaces the source MAC address included in the DHCP request with its own MAC address.
The router replaces the source IP address of the DHCP request with the IP address that is specified with the ip helper-address command.
The router replaces the broadcast destination IP address of the DHCP request with the unicast IP address that is specified with the ip helper-address command.
The router replaces the unicast destination IP address of the DHCP request with the unicast IP address that is specified with the ip helper-address command.
The router replaces the source MAC address included in the DHCP request with its own MAC address.
The router replaces the source IP address of the DHCP request with the IP address that is specified with the ip helper-address command.
The router replaces the broadcast destination IP address of the DHCP request with the unicast IP address that is specified with the ip helper-address command.
The router replaces the unicast destination IP address of the DHCP request with the unicast IP address that is specified with the ip helper-address command.
13. A client computer is set up for DHCP and needs an IP configuration. During the DHCP client configuration process, whichresponse will enable the client to begin using the assigned address immediately?
DHCPACK
DHCPREQUEST
DHCPOFFER
DHCPDISCOVER
DHCPACK
DHCPREQUEST
DHCPOFFER
DHCPDISCOVER
14.
Refer to the exhibit. An administrator wants to ensure that CEF is functioning properly on the switches between hosts A and B. If the administrator wants to verify the CEF FIB table entry for the route 10.10.5.0/24 on Sw_MLSA, what should the adjacency IP address be?
10.10.10.1
10.10.10.2
10.10.5.1
10.10.5.2
Refer to the exhibit. An administrator wants to ensure that CEF is functioning properly on the switches between hosts A and B. If the administrator wants to verify the CEF FIB table entry for the route 10.10.5.0/24 on Sw_MLSA, what should the adjacency IP address be?
10.10.10.1
10.10.10.2
10.10.5.1
10.10.5.2
15. Which three events will cause the Forwarding Information Base (FIB) table to be updated? (Choose three.)
An ARP entry for the destination next hop changes, ages out, or is removed.
The FIB table is cleared with the clear fib adjacency * command.
The routing table entry for the next hop changes.
The IP packets have an expiring TTL counter.
The TCAM table is flushed and reactivated.
The routing table entry for a prefix changes.
An ARP entry for the destination next hop changes, ages out, or is removed.
The FIB table is cleared with the clear fib adjacency * command.
The routing table entry for the next hop changes.
The IP packets have an expiring TTL counter.
The TCAM table is flushed and reactivated.
The routing table entry for a prefix changes.
16. Which condition will cause a packet to be process-switched instead of CEF switched?
packets that are switched to an outgoing interface with an outbound ACL applied
packets with a destination interface that is chosen by a routing protocol
packets that need to be fragmented on the outgoing interface
packets with a destination interface that is chosen by a static route
packets that use TCP header options
packets that are switched to an outgoing interface with an outbound ACL applied
packets with a destination interface that is chosen by a routing protocol
packets that need to be fragmented on the outgoing interface
packets with a destination interface that is chosen by a static route
packets that use TCP header options
17. Which statement is true about the CEF forwarding process?
The FIB table contains the Layer 2 rewrite information.
Adjacency table lookups use the closest Layer 3 prefix match.
The adjacency table eliminates the need for the ARP protocol.
After an IP prefix match is made, the process determines the associated Layer 2 header rewrite information from theadjacency table.
The FIB table contains the Layer 2 rewrite information.
Adjacency table lookups use the closest Layer 3 prefix match.
The adjacency table eliminates the need for the ARP protocol.
After an IP prefix match is made, the process determines the associated Layer 2 header rewrite information from theadjacency table.
18. What is true about TCAM lookups that are associated with CEF switching?
TCAM includes only Layer 3 lookup information.
A single TCAM lookup provides Layer 2, Layer 3, and ACL information
TCAM lookup tables are used only for the Layer 3 forwarding operation.
TCAM lookup tables are used only for the rapid processing of ACLs within CEF.
TCAM includes only Layer 3 lookup information.
A single TCAM lookup provides Layer 2, Layer 3, and ACL information
TCAM lookup tables are used only for the Layer 3 forwarding operation.
TCAM lookup tables are used only for the rapid processing of ACLs within CEF.
19.
Refer to the exhibit. What additional configuration is required for host A to receive IP configuration from the DHCP server?
The ip address dhcp command is required on interface Fa0/0.
The ip dhcp information option command is required on interface Fa0/1.
The ip helper-address 10.1.2.10 command is required on interface Fa0/0.
The ip forward-protocol 37 global configuration command is required to forward DNS requests to IP address 10.1.2.10.
The ip forward-protocol 67 global configuration command is required to forward DHCP requests to IP address 10.1.2.10.
The ip forward-protocol 69 global configuration command is required to forward TFTP requests to IP address 10.1.2.10.
Refer to the exhibit. What additional configuration is required for host A to receive IP configuration from the DHCP server?
The ip address dhcp command is required on interface Fa0/0.
The ip dhcp information option command is required on interface Fa0/1.
The ip helper-address 10.1.2.10 command is required on interface Fa0/0.
The ip forward-protocol 37 global configuration command is required to forward DNS requests to IP address 10.1.2.10.
The ip forward-protocol 67 global configuration command is required to forward DHCP requests to IP address 10.1.2.10.
The ip forward-protocol 69 global configuration command is required to forward TFTP requests to IP address 10.1.2.10.
20.
Refer to the exhibit and the show ip cef output. What can be concluded from the output?
The output validates that the CEF FIB entry for 10.10.5.0/24 is correct.
The cached adjacency address is 10.10.10.1.
The next hop address is 10.10.10.1.
The output shows that packets destined to 10.10.5.0/24 have not been processed by CEF.
Refer to the exhibit and the show ip cef output. What can be concluded from the output?
The output validates that the CEF FIB entry for 10.10.5.0/24 is correct.
The cached adjacency address is 10.10.10.1.
The next hop address is 10.10.10.1.
The output shows that packets destined to 10.10.5.0/24 have not been processed by CEF.